
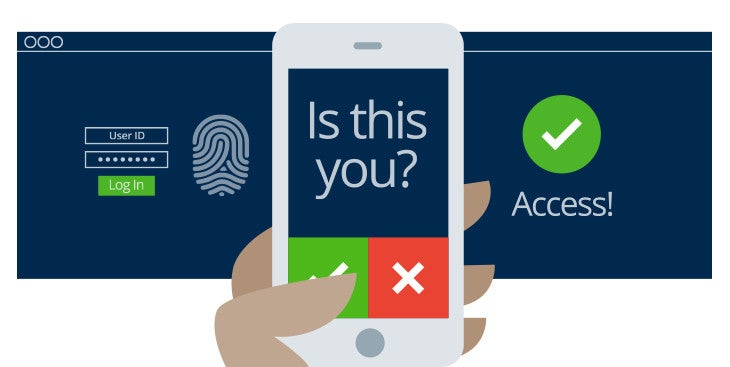
Multifactor Authentication is the need of every business that works around sensitive data and users’ personal information. The system adopts a layered approach for security, which makes it difficult for individuals to gain access to the data.
By providing an extra level of security besides the phone password, Multifactor Authentication System (MFA) has become the must-have feature of apps related to payments, enterprise apps related to viewing or retracting data from the cloud.
Let us take a deep dive into the concept of MFAs, highlighting the four ways you can implement Multifactor Authentication in your mobile app. We will also throw some light on the challenges, both technical and user-specific, that you should prepare to be encountered with.
But, before we go in further, let us look at what Multifactor Authentication System actually means.
What is Multifactor Authentication System (MFA)?
Multifactor authentication or MFA, as it is commonly called, works around providing an added layer of security that ensures that users are providing more than a single piece of evidence for their identification. It usually requires a blend of something which the user knows, like pins, passwords, something which the user has, like cards, phone, or something that they inherit like a Fingerprint scan or Retina scan.
Now, there are four ways through which you can implement MFAs in your Mobile Application. Let us look at each of them in terms of the process they take the users through.
Ways to Implement Multifactor Authentication in a Mobile App
1. Time-Based OTP
OTP comprises the creation of a one-time password from a shared secret key and the present timestamp with the help of the exact type of cryptographic function. OTP involves the enrollment and login processes.
Here’s a detail on both the processes –
Enrollment Process:
- Users log in to the app with their passwords and username
- If the credentials are found valid, the next stage is to enable the two-factor authentication
- The shared key is then requested, which can be either text-based or QR code
- The key is stored by the app which implements OTP like Auth0 Guardian or Google Authenticator.
- The two-factor authentication is then enabled.
Next comes the Login process:
- User logs into the app
- If their credentials are valid, they are directed to a form where they have to put in one-time code generated with Auth0 Guardian or Google Authenticator
- The server then verifies that the code is valid and authenticates the user
2. SMS
The process of multifactor application through SMS also involves enrollment and the login stage.
Enrollment Process:
- User logs in to an application with username and password.
- They are asked to enter an active phone number
- A distinctive one-time code is then generated on the app server and is sent to the user’s phone number.
- They then enter the code in-app, thus enabling multifactor authentication
Login Process:
- User logs in to the application with their user-id and password.
- A distinctive one-time code is then generated on the app server and is sent to the user’s phone number.
- The user enters the code in-app.
- If found valid, the user gets authenticated and the session gets initiated.
3. E-Mail
- User logs in to an application with their user-id and password.
- A distinctive one-time code is then generated on the app server and is sent to the user’s email id
- They retrieve the code from their email and feeds it into their app.
- If found valid, the user is then authenticated and the session gets initiated.
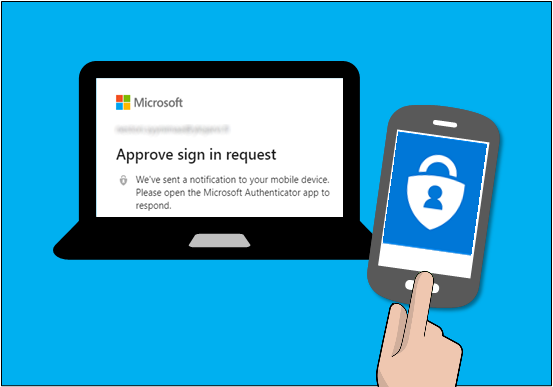
4. Push Notifications

- User logs in to an application with their user-id and password.
- Usually, the push notifications mechanism works with applications like Auth0 Guardian. Once the details are entered, a push notification is then sent by the Guardian app to your app.
- The notification is a login request.
- On the backend, this includes data like the OS, application name, and browser used while making the request, the precise location, and the date when the request is being made.
- The user then asserts the request they have received through push notification and gets logged in.
Now that you know the ways you can implement MFAs in your mobile app, let us look into the challenges that come associated.
Challenges Associated with Multifactor Authentication System
It is very difficult to implement the system in your mobile app without the support of a Mobile App Development Company that specializes in providing extensive quality assurance in terms of mobile app security. While this is from the business front, every added security layer comes with more work for the users. It can lead to frustration when users are made to repeat multiple steps every time they have to do a task.
But the challenges that the system comes with are very minimal in front of the benefits that they have to offer when it comes to giving the users a safe transaction environment, amidst the soaring data breach incidents.
Want to take your Mobile App Security to the next level? Contact our Team of Mobility Experts, today.


