With geopolitical tension rising in certain parts of the world along with the ambitions of cyber attackers, coming up with a holistic strategy to protect the nation’s critical infrastructure has become a priority for the enterprises handling them. Imagine what would happen if the nuclear plants or the space agencies of a country were hit by a cyber attack. The disruption caused due to a successful cyber attack on a nation’s critical agencies can be far-reaching. It has the potential of causing a major loss of money, time, and even lives. This can be illustrated by a recent incident.
After the release of the largest-ever compilation of breached usernames and passwords, COMB, a cyber attacker wrongfully entered the Oldsmar (Florida) water plant’s computer systems to poison the city’s water supply by changing its pH to dangerously acidic levels. Even though the attack was thwarted before completion, this incident has opened our eyes to the dangerous reality of such an attack being successfully executed in the future.
Tomorrow, this attack can take place in the form of manipulation of boiler pressure in a thermal power plant or a ransomware attack on the country’s top-tier healthcare institutions. All of such attacks are not only potentially life-threatening but also pose a huge risk of material damage.

Other Cyber Incidents Around the World Involving Critical Infrastructure
In February 2020, Saudi authorities reported that their public petroleum and natural gas company Saudi Aramco has seen an increase in cyber attack attempts. This public enterprise suffered a huge cyber attack back in the year 2012 when Shamoon Virus hit the facility and damaged around 30,000 computers.
A few months back, New Zealand’s central bank suffered a huge data breach, where commercially and individually sensitive information was stolen by cyber attackers.
In another event, an electricity grid in the state of Maharashtra (India) was hit by a cyber attack that resulted in a power outage. This incident took place in the month of October 2020 and the authorities suspect Chinese involvement in it.
Discussing the Deterrent
In today’s world, there is cut-throat competition between countries for production and use of resources. Therefore, it is all the more important for enterprises handling and managing the critical infrastructure to adopt a multipronged approach while planning a defense against cyber attacks.
At the organizational level, some of the following measures can help in stopping cyber attacks from affecting the enterprise-
- Access Management – Access management is the first basic measure that organizations should take to protect their control systems. Identity Access Management (IAM) in databases and other important IT infrastructure is necessary to limit access and prevent the misuse or leak of information.
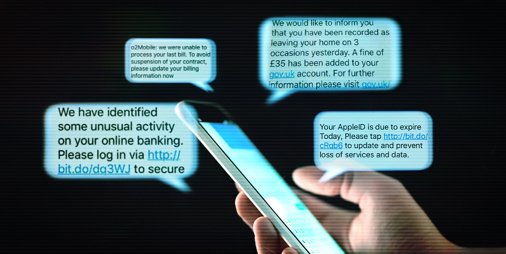
- Awareness as Defense – One very effective way of preventing cyber attacks on an enterprise is to train the employees in the basics of cyber security. Cyber aware employees form a major defense against attempted cyber attacks on the enterprise.

- Email Domain Security – To ensure the security of an organization, it is imperative to address the cyber threats originating from its email domain. Using email domain security tools like KDMARC can be very effective in stopping spoofing of the email domain to protect the enterprise against spear-phishing and BEC attacks.
- Data Backup – Frequent data backup in offline locations in a segmented manner is the best approach to defend against ransomware attacks.
- Incident Response – Use of incident response tools can facilitate quick detection of and response to a cyber attack. A phishing incident response tool like Threat Alert Button (TAB) can be quite helpful in identifying and removing phishing emails from the employees’ inboxes.
- Strong Password Policy – Employees should be encouraged to use strong passwords. This applies to both their work emails and other credentials used for accessing information and operations of critical systems in the enterprise.