Building a revolutionary mobile application is only the first step in mobile app development. Once you’ve built an app, there are thousands of mandatory processes that follow app development. One of those many crucial steps in mobile app security.
In this article, we will explore what are the essential mobile app security practices that you ought to implement after the development is finalized.
Over the last decade, we all have witnessed how the mobile app development industry has grown but so have cybercrimes. And these crimes have led us to a stage where it is not possible to submit an app to Play Store or App Store without taking certain measures to secure it.
However, getting towards what the security measures entail, we first need to understand why there is a need for taking these actions and what are the potential app security issues that plague the mobile app development industry. For a real-life estimate, let us look at the facts:
There is still more to mobile app security than safeguarding them against malware and threats. Let us first identify some of the OWASP mobile app security threats to understand the security measures better.
Why do we need Mobile App Security: Potential Threats & Their Solutions
The threats that present themselves in the app development world although are malicious, can be solved with simple steps to securing a mobile application. Let us take a look at what are the major mobile app security issues.
1. Faulty server controls:

The communications that take place between the app and user outside the mobile phone device happen via servers. And such servers are primary targets of hackers throughout the world. The main reason behind the vulnerability of a server is because sometimes developers overlook the necessary server-side security into account. This may happen due to a lack of knowledge about security considerations for mobile applications, small budgets for security purposes, or the vulnerabilities caused due to cross-platform development.
Solution:
The most crucial step in safeguarding your servers is to scan your apps with the help of automated scanners. These scanners can, otherwise, be used by hackers to dig out vulnerabilities in your apps and exploit them. Automated scanners will surface the common issues and bugs which are easy to resolve.
2. The absence of Binary protection:

This is also one of the prime OWASP app security issues to address because if there is a lack of Binary protection for a mobile app, any hacker or an adversary can easily reverse engineer the app code to introduce malware. They can also redistribute a pirated application of the same and inject it with a threat also. All of this can lead to critical issues such as data theft and damage to brand image and resultantly revenue loss.
Solution:
To safeguard Binary files, it is important to deploy binary hardening procedures. As a part of this procedure, binary files are analyzed and accordingly modified to protect them against common mobile app security threats. This procedure fixes the legacy code without involving the source code at all. It is crucial to ensure security coding for the detection of jailbreaks, checksum controls, debugger detection control, and certificate pinning while working on mobile app security processes.
3. Data Storage Insecurity:

Another big loophole that is common in Mobile app security is the absence of a safe data storage system. In fact, it is common for mobile app developers to rely upon client storage for internal data. However, during the possession of a mobile device by a rival, this internal data can be very easily accessed and used or manipulated. This can lead to several crimes like identity theft or PCI (external policy violation).
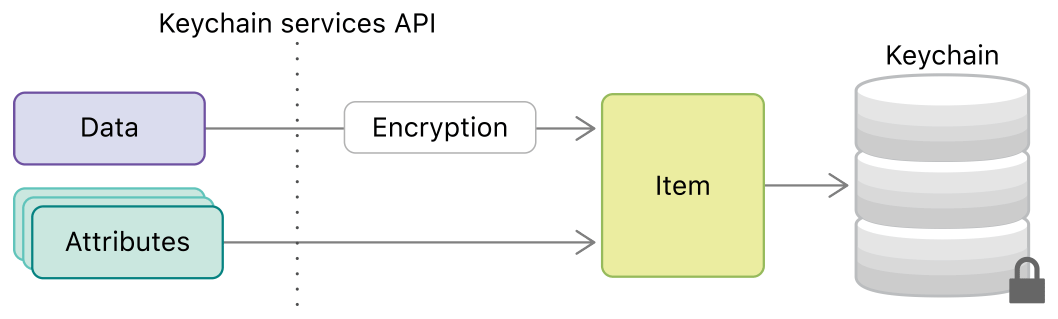
Solution:
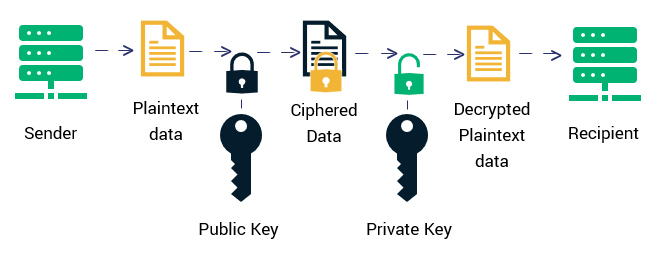
One of the app security measures to consider here is to build an additional encryption layer over the OS’s base-level encryption. This gives a tremendous boost to data security.
4. Inadequate protection for Transport layer:

The transport layer is the pathway through which data transfer takes place between the client and the server. If the right mobile app security standards are not introduced at this point, any hacker can gain access to internal data to steal or modify it. This leads to severe crimes like identity thefts and frauds.
Solution:
To reinforce transport layer security, you should incorporate SSL Pinning in iOS and Android apps. Along with this, you can use industry-standard cipher suites instead of regular ones. Additionally, avoiding the exposure of user’s session ID because of mixed SSL sessions, alerting the user in case of an invalid certificate, using SSL versions of third-party analytics are common practices that can savethe users from a dangerous breach of security.
5. Unintended Leakage of data:
Unintended data leakage happens when critical mobile applications are stored in vulnerable locations on the mobile device. For example, an app is stored where it can easily get accessed by other apps or devices which ultimately results in the data breach of your app and unauthorized data usage.
Solution:
Monitoring common data leakage points such as logging, app background, caching, Browser cookie objects, and HTML5 data storage.
Besides these 5 mobile development security threats, there are some other commonly occurring roadblocks in the way of building secure mobile apps. Here they are:
- Absence of multi-factor authentication – The process provides multiple layers of security before letting a person inside the application. It could be answering a personal question, OTP, SMS configuration, or other measures. The absence of multifactor authentication can lead to several issues which makes it a crucial part of answering how to make an app secure.
- Inability to encrypt properly – A important element of mobile application security best practices is ensuring proper encryption. The inability of it can lead to code theft, intellectual property theft, privacy violation, among multiple other issues.
- Malicious code Injection – User-generated content such as forms is often overlooked as a threat. Suppose a user adds in their id and password, the app then communicated with the server-side data to authenticate the information. Now the apps which do not restrict the character a user inputs open themselves to the risk of injecting code to access the server.
- Reverse engineering – It is every secure mobile application development nightmare. The approach can be used to show how an app works in the backend and reveal the encryption algorithms while modifying the source code, etc.
- Insecure data storage – insecure data storage can happen in multiple places inside an app – cookies, binary data store, SQL database, etc. If a hacker gets access to the database or device, they can alter legitimate apps to take out information to the machines.
After seeing the general threats which plague all the mobile applications and some of the Best mobile app security practices to follow for avoiding these issues, let us move on to the specifics about the Android and iOS mobile application security.
How to Make Android Apps Secure?
Some of the effective Android app security best practices to opt are:-
Encryption of data on External Storage –

Generally, the internal storage capacity of a device is limited. And this drawback often coerces users to use external devices such as hard disk and flash drives for safekeeping of the data. And this data, at times, consists of sensitive and confidential data as well. Since the data stored on the external storage device is easily accessible by all the apps of the device, it is very important to save the data in an encrypted format. One of the most widely used encryption algorithms by mobile app developers is AES or Advanced Encryption Standard.
Using Internal Storage for Sensitive Data –

All the Android Applications have an internal storage directory. And the files stored in this directory are extremely secure because they use MODE_PRIVATE mode for file creation. Simply put, this mode ensures that the files of one particular app cannot be accessed by other applications saved on the device. Thus, it is one of the mobile app authentication best practices to focus upon.
Using HTTPS –

The communications that take place between the app and the server ought to be over an HTTPS connection. Numerous Android Users often are connected to several open WiFi networks in public areas and using HTTP instead of HTTPS can leave the device vulnerable to many malicious hotspots which can easily alter the contents of HTTP traffic and make the device’s apps behave unexpectedly.
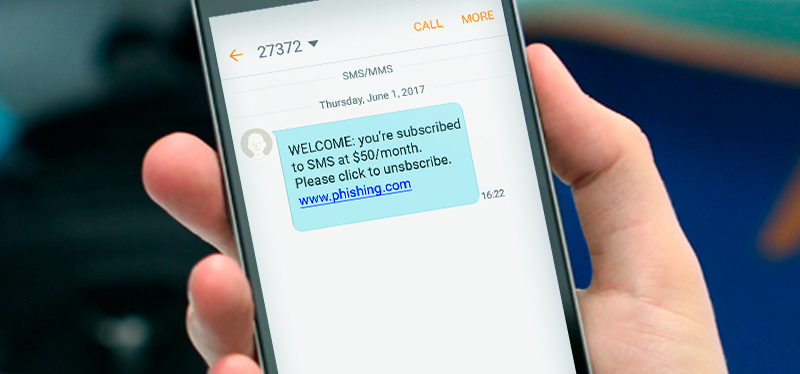
Using GCM instead of SMS –
![The Ultimate Guide to Push Notifications [2020] - WebEngage](data:image/svg+xml;base64,PHN2ZyB3aWR0aD0iMSIgaGVpZ2h0PSIxIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciPjwvc3ZnPg==)
In the time when Google Cloud Messaging or GCM did not exist, SMS was used in order to push data from servers to apps but today, GCM is used largely. But if you still have not made the switch from SMS to GCM, you must. This is because SMS protocol is neither safe nor encrypted. On top of it, SMS can be accessed and read by any other app on the user’s device. GCM communications are authenticated by registration tokens which are regularly refreshed on the client-side and they are authenticated using a unique API key on the server-side.
Other major mobile app development security best practices can include, Validation of User input, Avoiding the need for personal data, and usage of ProGuard before publishing the app. The Idea is to secure app users from as much malware as possible.
How to Make iOS Apps Secure?
Some of the iOS app security best practices to follow are:-
Storage of Data –

To greatly simplify your app’s architecture and improve its security, the best way is to store app data in memory instead of writing it on a disk or sending it to a remote server. Although if storing the data locally is your sole option, there are multiple ways to go:-
Keychain:

The best place to store small amounts of sensitive data which doesn’t need frequent access is Keychain. Data that is stored in keychains is managed by the OS but is not accessible by any other application. – Caches: If your data does not need to be backed up on iCloud or iTunes then you can store the data in the Caches directory of the application sandbox. – Defaults system: The defaults system is a convenient method for storing large amounts of data.
Networking security :

Apple is known for its security and privacy policies and for years, it has worked to reach this level. A few years ago, Apple had introduced App Transport Security which enforces third-party mobile apps to send network requests over a more secure connection, i.e., HTTPS.
Security of Sensitive Information –

The majority of mobile apps use sensitive user data such as address book, location, etc. But as a developer, you need to make sure that all the information that you’re asking the user for is, in fact, necessary to access and more importantly, to store. So, if the information you require can be accessed through a native framework, then it is redundant to duplicate and store that information.
We have now seen both Android and iOS mobile app security Practices for a Hack-Proof App. But no development can be so easy as it is written about. There are always certain challenges that are faced during a process. Let’s move forward and learn about the challenges which are faced and solved by almost every top app development companies in USA.
Challenges Associated With Mobile App Security
There is a proven record of how vulnerable mobile apps can be if not enough measures are taken for their security from external malware. Following are the challenges that can arise anytime if the mobile app security testing is not completed as per the requirement.
Device Fragmentation –

There are essential processes to be followed before the release of an application on the app stores. It is necessary to diversity of devices that cover different resolutions, functionalities, features, and limitations into your mobile app testing strategies. Detection of Device specific vulnerabilities can put the app developers one step ahead in app security measures. Not only devices but different versions of popular OS’s is an important step to cover before the app release to cover all the possible loopholes.
Weak Encryptions –

In the case of weak encryption, a mobile device is vulnerable to accepting data from any available device. Attackers with malware are in constant search for an open-end in public mobile devices and your app can be that open end if you do not follow a strong suit of the encryption process. So, investing your efforts into strong encryption is also one of the finest ways to make a hack-proof mobile app.
Weaker hosting controls –

It happens mostly during the development of a business’s first mobile app, which usually leaves the data exposed to the server-side systems. Therefore, the servers which are being used to host your app must have enough app security measures to avoid any unauthorized users from accessing important data.
Checklist for Mobile Application Security Guidelines
There are a number of things that every mobile app development company follows when they build secure applications. Here is a checklist that we commonly follow –
- Use server-side authentication
- Use cryptographic algorithms
- Ensure user inputs meet check standards
- Create threat algorithms to back data
- Obsfucation to stop reverse engineering
There are many ways to make a hack proof mobile app, through a mobile app security audit, against the attacks from unknown sources and no amount of security measures can ever be enough. Looking into mobile app development security best practices is one way to go about it. Today, the digital world is out in the open for everyone’s use and no user is ever safe enough from malware and security breaches but these measures ensure that your personal data is safe in your digital devices.





























![The Ultimate Guide to Push Notifications [2020] - WebEngage](https://content.webengage.com/wp-content/uploads/sites/4/2017/09/What-is-a-Push-Notification.png)