Vulnerabilities are the anomalies such as programming errors or configuration issues of the system. Attackers exploit the weaknesses in the system and can, in turn, disrupt the system. If these vulnerabilities are exploited, then it can result in the compromise of confidentiality, integrity as well as the availability of resources that belong to the organization.
How Can We Detect and Prevent These Vulnerabilities?
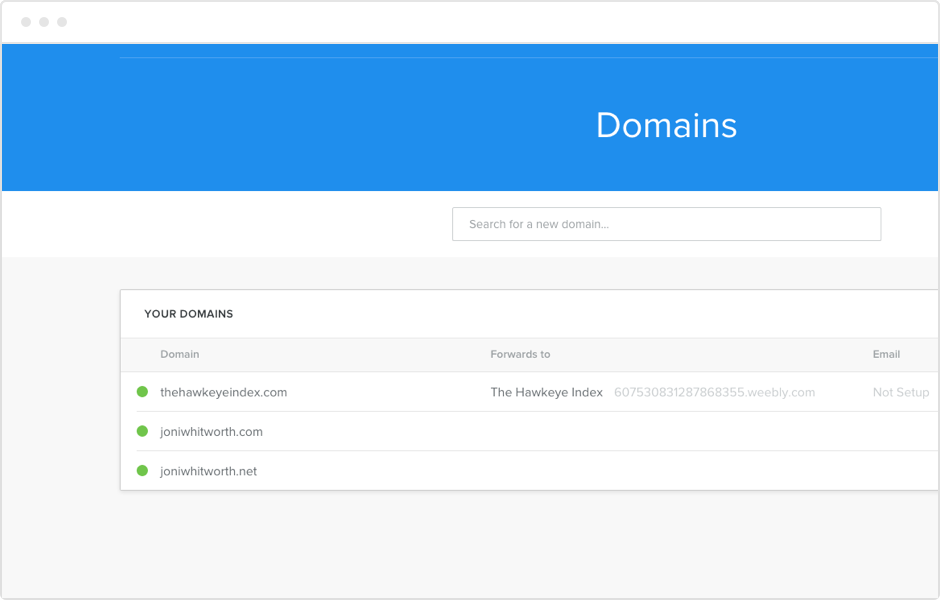
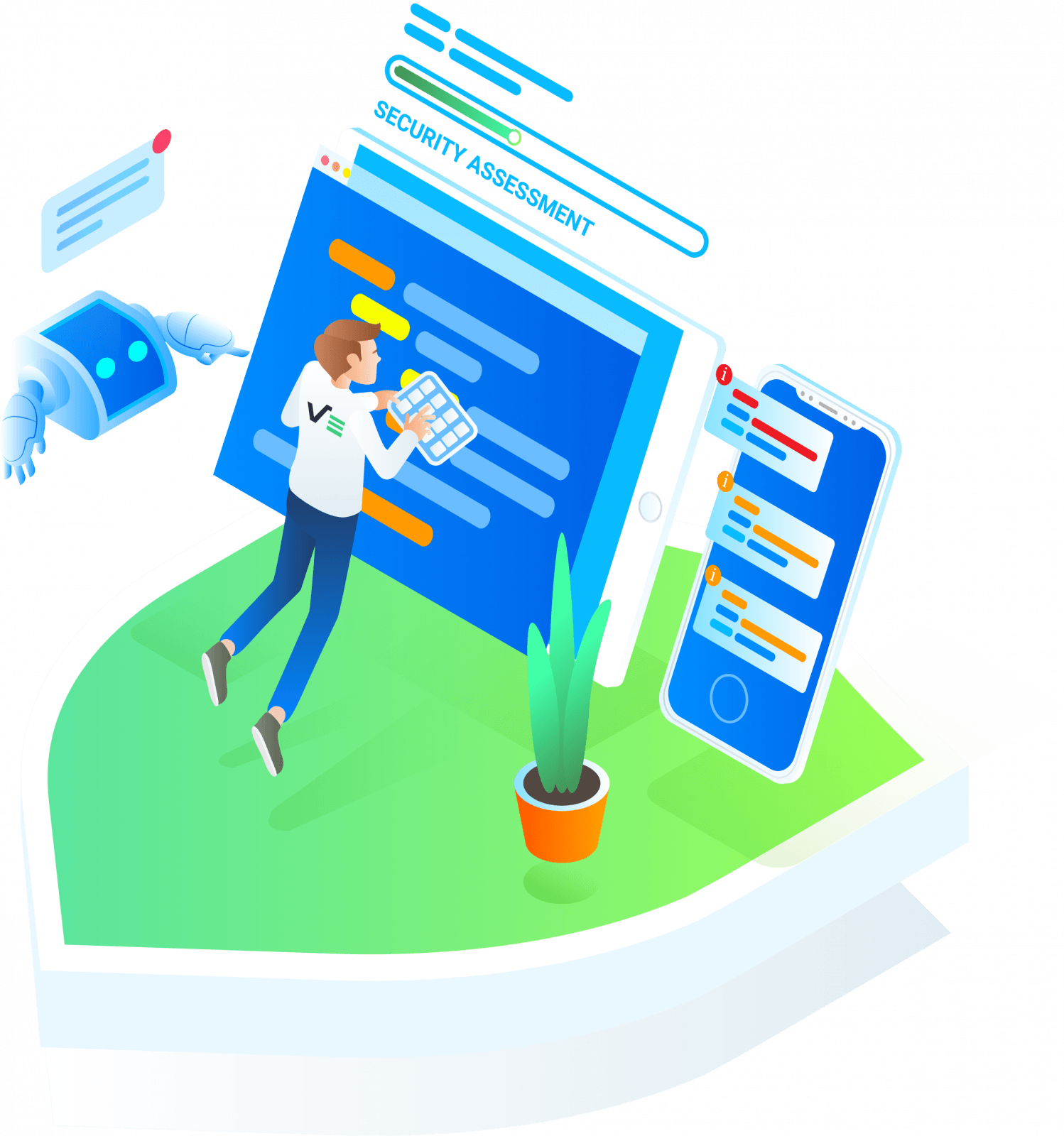
Vulnerability assessment is the risk management process that defines, identifies, classifies, and prioritizes vulnerabilities within computer systems, applications as well as network infrastructures. This helps the organization in conducting the assessment with the required knowledge, awareness, and risk posture for understanding the cyber threats. Vulnerability assessment is conducted in two ways.
Types of Vulnerability Assessment
Automated Testing

Automated tools such as Vulnerability scanning tools scan applications to discover cyber security vulnerabilities. These include SQL injection, Command Injection, Path Traversal, and Cross-Site scripting. It is a part of Dynamic Application Security Testing that helps in finding malicious code, application backdoors as well as other threats present in the software and applications.
Manual Testing

Manual testing is based on the expertise of a pen-tester. They are the experts that dive deep into the infrastructure that will help them in finding out the vulnerabilities that cyber attackers can exploit.
Following are the types of vulnerability assessment and penetration testing:
Different Types of Manual Testing
- Application Security Testing

It is the process of testing and analyzing a mobile or web application. This methodology helps pen-testers in understanding the security posture of websites and applications.
The application security testing process includes:
-
- Password quality rules
- Brute force attack testing
- User authorization processes
- Session cookies
- SQL injection
- Server Security Testing
Servers contain information including the source code of the application, configuration files, cryptographic keys as well as other important data. Pen-testers perform an in-depth analysis of the server in the server security testing. Based on this analysis, testers perform an approach to mimic real-time cyber attacks.
- Infrastructure Penetration Testing
Infrastructure penetration testing is a proven method to evaluate the security of computing networks, infrastructure as well as the weakness in applications by simulating a malicious cyber attack.
- Cloud Security Testing
Every organization that keeps its platforms, customer data, applications, operating systems as well as networks over the cloud; must perform cloud security testing. Cloud security is essential for assessing the security of the operating systems and applications that run on the cloud. This requires equipping cloud instances with defensive security controls and regular assessment of the ability to withstand cyber threats.
- IoT Security Testing

With our increasing engagement with technology, we are becoming more advanced in incorporating technology with things that we use on a daily basis. Pen-testers are aware of the complexities and how cyber criminals exploit them.
IoT penetration and system analysis testing considers the entire ecosystem of IoT technology. It covers each segment and analyses the security of the IoT devices. The testing services include IoT mobile applications, communication, protocols, cloud APIs as well as the embedded hardware and firmware.
Which is the Better Method of Vulnerability Assessment?
Manual vulnerability assessment is better than vulnerability scanning tools since automated tools often give false results. This can seriously hamper the process of vulnerability assessment. Although automated tools make the assessment process faster and less labor-intensive, the tools are not capable of identifying vulnerabilities.
This can be far better done by observant pen testers who use systematic technology with years of experience. Manual vulnerability assessment requires time but, it is far more effective and accurate than vulnerability scanning tools. The reason behind preferring manual assessment is the lack of an in-depth understanding of the system to discover vulnerabilities. Therefore, it is always better to consult a leading cyber security company for investing in VAPT services that can help you strengthen your organization’s security infrastructure.























 The word ‘impersonation’ refers to the act of pretending to be another person for a purpose or fraud. Impersonation attacks are a form of
The word ‘impersonation’ refers to the act of pretending to be another person for a purpose or fraud. Impersonation attacks are a form of 


/cdn.vox-cdn.com/uploads/chorus_asset/file/19349208/jbareham_191158_ply0958_decade_anime.jpg)