With the rapid development in technology and ever-increasing internet users, cyber security plays a critical role in every industry. Securing the IT infrastructure in an enterprise helps in maintaining smooth workflow and consistent business operations.
In recent times, cyber crimes have become extremely sophisticated and threat actors have come up with new ways to obtain access to an organization’s systems and sensitive information. All throughout 2020, everyone was battling to overcome the onslaught of challenges brought by the pandemic.
However, cyber criminals saw an opportunity and wholeheartedly exploited the panic and chaos caused by the pandemic to fill their own pockets. And these criminals took no time to launch back to back cyber attacks during the pandemic.

These threat actors left no stone unturned to target the vulnerable companies that weren’t prepared to support a remote workforce securely. As a number of well-established companies became victims to various cyber attacks, 2020 witnessed several security incidents making the headlines.
Since companies are not willing to compromise with the health of their employees, remote working is expected to continue in 2021 and beyond. But the question is, how do companies survive the fight against cyber crime and secure their employees while overcoming the challenges posed by COVID-19?
Cyber Risks and Lack of Security Awareness Among Employees
Often organizations focus on upgrading the hardware and technologies to stay protected against cyber threats. In doing so, organizations spend millions of dollars on the latest security patches and upgrades. But just like our computers, humans store, process, and transfer information too.
Yet, if you compare the amount of time and money an organization spends on securing its computers and other electronic devices to the resources it focuses on securing its employees, you’ll see how huge the difference is!
Organizations typically invest a lot in installing antivirus and spyware software as well as upgrading the operating systems, applications, and browsers. Additionally, every company has help desks, support teams, and security technical teams to maintain all this software and hardware. But how much does an organization spend on securing employees? Very less.
Cyber security has become a massive issue in both private and government institutions. Looking into the core of the issue, it is not really about the technology or the systems. Technology and systems have become increasingly secure over the years.
Employees are the actual issue. Even though it is unintentional, most cyber attacks are caused by human error, whether it is a careless click on an unsolicited link or an innocent downloading of a corrupted file.
How to Fix these Cyber Security Loopholes?
It may sound controversial, but the security teams are the last line of defense within an organization. Even though these teams face many cyber security challenges, it is the employees who form the first line of defense.
According to a report by IBM Security, human error is the main cause of 24% of all data breaches.
Therefore, it is imperative for every organization to train the employees to be aware of the prevalent cyber threats. This does not mean that organizations should implement such heavy security measures that will just create chaos and difficulties for the employees.
Rather, every organization should come up with a solution that makes the day jobs as easy as possible for the employees while making their IT infrastructure as secure as possible.
Here are some effective measures you can take to secure your organization:
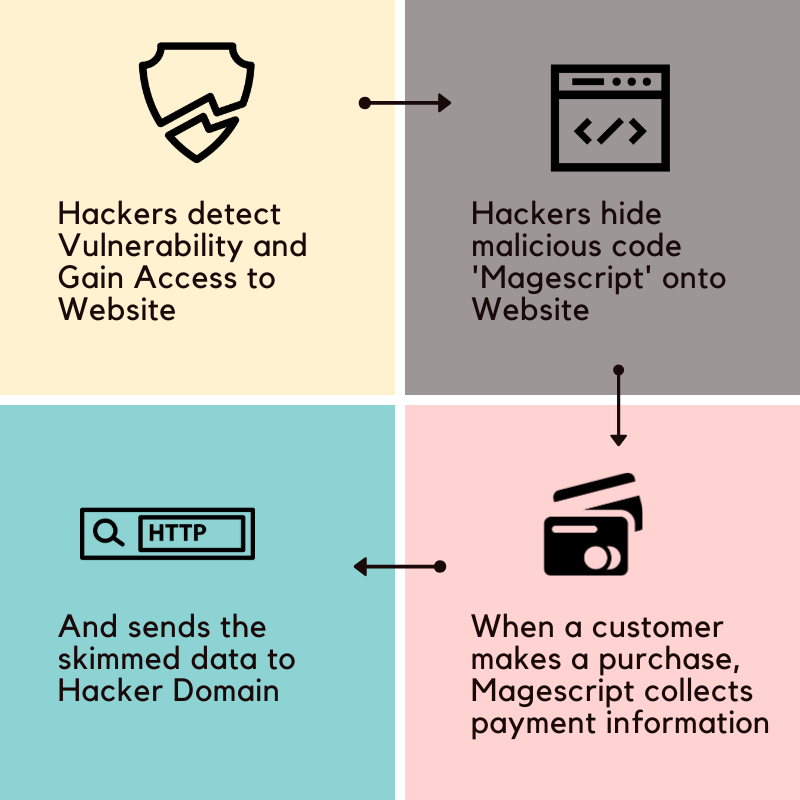
- Discover: Start looking from a risk management perspective. Find out if there are any flaws in the organization’s cyber security framework. Conduct services like VAPT to discover and identify the loopholes within your organization’s network and IT infrastructure.
- Practice healthy cyber hygiene: Implement basic cyber security protocols. Enforce a strong password policy, enabling multi-factor authentication for verification, using secure Wi-Fi, encrypting sensitive data, and regularly updating the systems with the latest security patches.
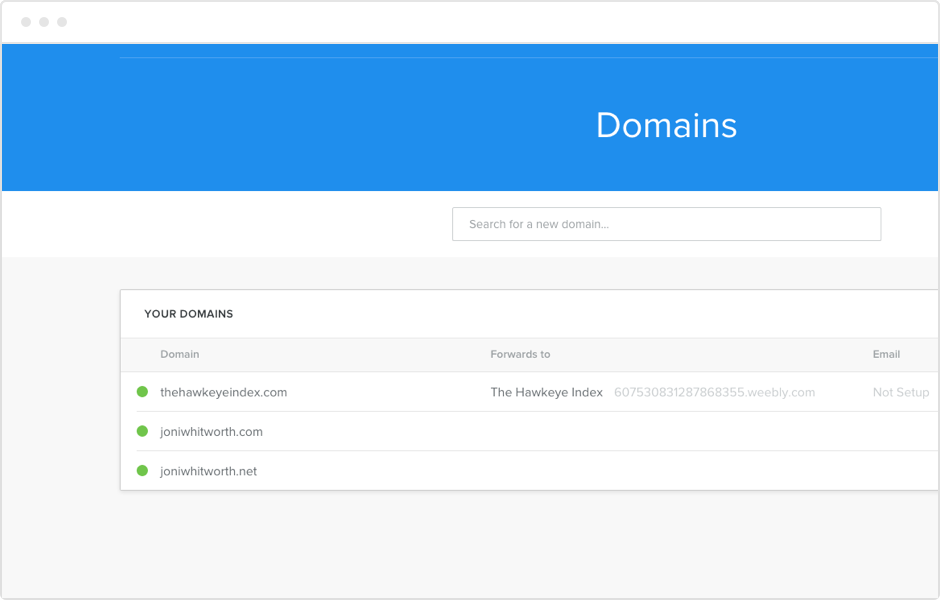
- Lookout for malicious links: Think carefully before clicking on a link or downloading an attachment from an unknown source. An email can sometimes be from a threat actor impersonating a trusted individual. To protect yourself against malicious actors impersonating your email domain, set up tools like KDMARC and defend your domain against forgery.
- Set up a firewall: As the name suggests, a firewall is a wall between the computer and the internet. It acts as the gatekeeper for all incoming and outgoing network traffic. Setting up a firewall protects the internal networks of your business against cyber threats.
- Update on the latest risks: Keep up with the latest cyber hacks and threats news. It helps your organization stay up-to-date with the latest cyber security-related news. It also provides you with the cyber security preventive measures that your organization can adopt to avoid becoming a victim.
- Train Employees: Educate employees to recognize social engineering attacks such as phishing, vishing, smishing, etc. To be more aware of the cyber threats evolving around the world and how to react when needs arise.
The Ultimate Solution to Make Employees Cyber Secure

There are several steps an organization can take to protect itself against cyber threats. However, it all comes down to how strong is your organization’s first line of defense – the employees. It has become essential for organizations to provide cyber security awareness training to their employees.
You can opt to educate your employees with tools that offers the most effective security awareness training materials. The tool generates awareness amongst employees about the common cyber threats wreaking havoc around the world.






 The word ‘impersonation’ refers to the act of pretending to be another person for a purpose or fraud. Impersonation attacks are a form of
The word ‘impersonation’ refers to the act of pretending to be another person for a purpose or fraud. Impersonation attacks are a form of 


/cdn.vox-cdn.com/uploads/chorus_asset/file/19349208/jbareham_191158_ply0958_decade_anime.jpg)