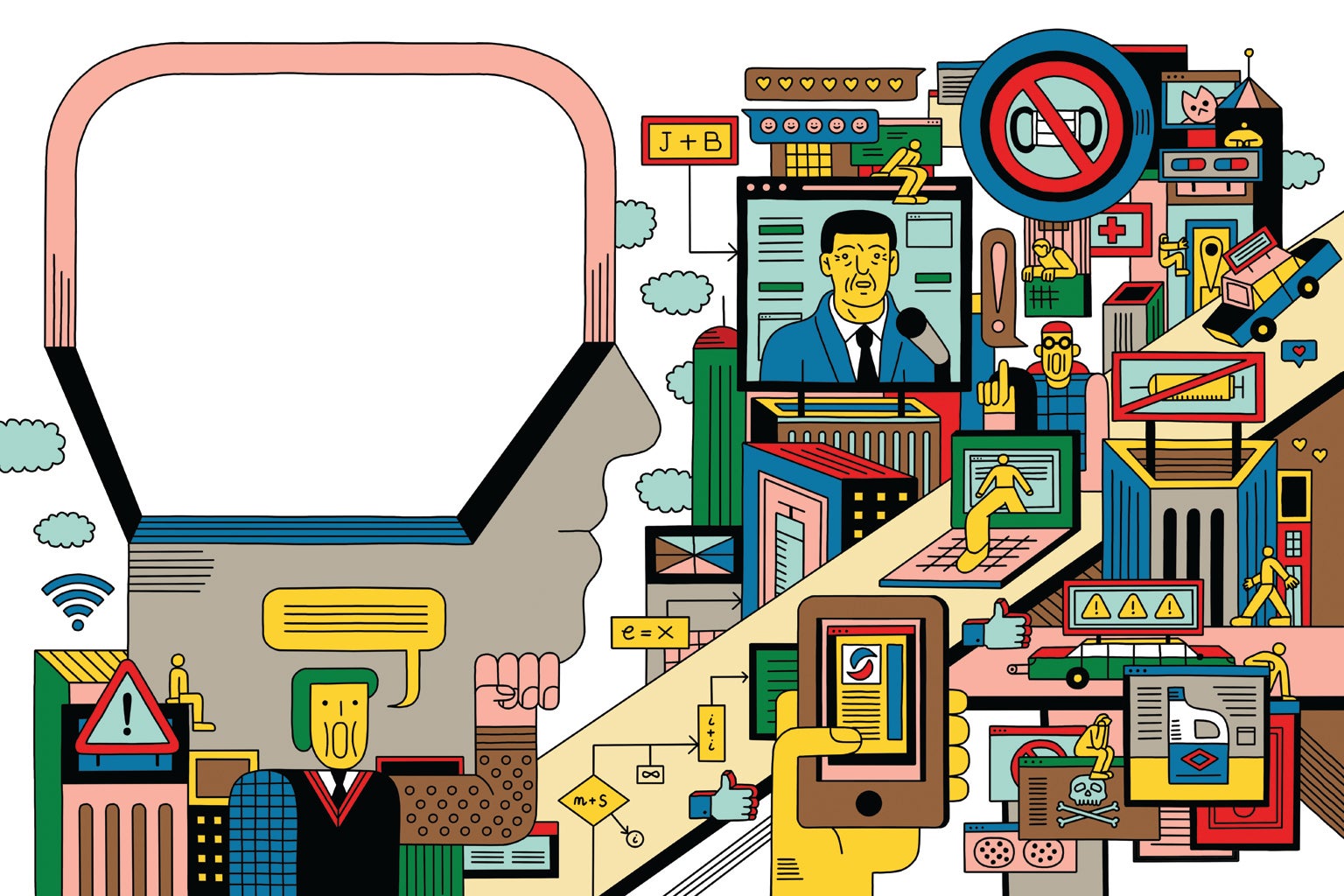
Are you using social media platforms on daily basis then you must be aware of its dark side impacts on your social life? Let’s talk and rethink about your personal safety before using these interactive internet based applications. As people use it to connect with far-flung friends and family members to send speedy messages to colleagues and can broadcast major and minor actions in your lives. This is also a basic platform for many businesses to collaborate or share information for instance; individuals can discuss an assignment with co-workers by means of a various social media messaging session. With advancement employers and schools are more and more using social media to reach out to possible employees and students as well.
According to the Bureau of Justice Statistics, more than 16 million US residents became victims of identity theft in 2012 alone. Keeping your passwords, financial, and other personal information safe and protected from outside intruders has long been a priority of businesses, but it’s increasingly critical for consumers and individuals to pay attention to data protection advice and use various top-notch practices to keep your personal information secure and protected. There is loads of information out on the internet there for consumers, families, and persons on protecting their bank credentials, sufficiently protecting desktop and laptop from hackers, malware, and other threats, and most excellent practices for using the Internet safely for personal safety. Protecting your individual information via various cybersecurity training programs can help lessen your menace of individuality theft.
Various conducts to secure your data:

- Maintain proper security on your PC, Mobiles and other electronic devices to secure your social life.
- Systematically store and arrange your personal information securely
- Ask questions before deciding to share your individual information
Practices for personal safety and Keeping Your Devices Secure
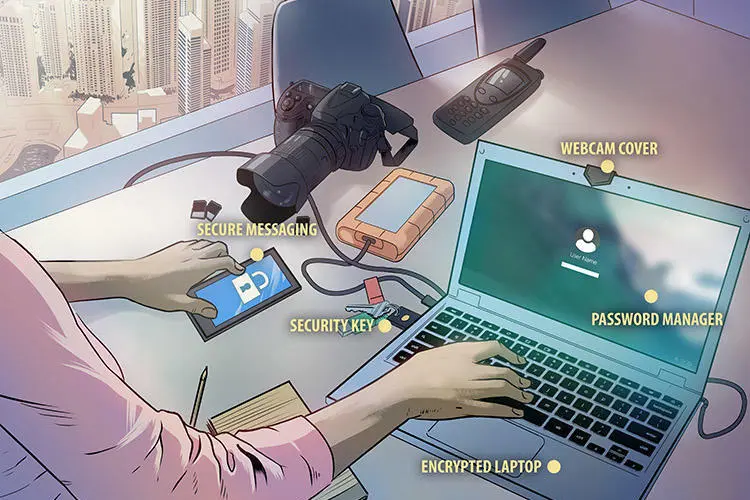
- Install good quality anti-virus software, anti-spyware software, and a firewall.
- Don’t open files which are not known to you or download programs sent by outsiders.
- Before sending personal information over your laptop on a public wireless check if your information will be protected.
- Keep financial information on your laptop only if necessary.
- Don’t use an automatic login feature on your bank accounts and emails that save your username and password.
- Delete mail that contains identifying information or account numbers or invalid transaction.
There is so much information that may make you get confused, principally if you’re not a tech-savvy. In order to mend these issues, you can adopt various straightforward best practices and tips for protecting your devices from threats or simply consult us via contact@anteelo.com and get various security tips to secure your social platforms.



















![Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager](https://dataprivacymanager.net/wp-content/uploads/2019/10/Data-Privacy-vs.-Data-Security.png)