What can be the cruelest but most effective way to test your employees if they are aware of the risks and preventions of a phishing attack? Godaddy, the world’s largest domain registrar and web-hosting company, simulated a phishing test for employees to increase alertness levels against phishing attacks.
On December 14, an email tucked underneath the snowflake banner with the words “GoDaddy HOLIDAY PARTY” from “Happyholiday@Godaddy.com” was sent to hundreds of Godaddy employees offering a holiday bonus. The message in the email said, “2020 has been a record for GoDaddy, thanks to you!”

“Though we cannot celebrate together during our annual Holiday Party, we want to show our appreciation and share a $650 one-time Holiday bonus!” it further added.
To ensure that the recipients receive the bonus, they were asked to fill in the personal details by December 18. But instead of receiving the bonus, two days later, almost 500 employees received an email from the company’s Chief Security Officer, Demetrius Comes.
Though many criticized the bonus offer in GoDaddy’s test as insensitive, companies do organize phishing simulation tests to educate employees on cybersecurity.
GoDaddy is not the first company this year to provide phishing email awareness for employees. Earlier this year, Tribune Publishing, a giant newspaper company in America, sent out a similar phishing email to the employees.
The email circulated by several employees on Twitter said the company was providing targeted bonuses between $5,000 to $10,000. Only to find out later that it was a phishing test sent from the company.
Why Should Organizations Run ‘Employee Phishing Test’?
Imagine the consequences, if GoDaddy’s phishing test was not a test but a real phishing attack from a hacker! Roughly 500 employees failed the test, so, almost 500 of them would have submitted their personal information to hackers. This could have led to a complete disaster for the company.

Providing this kind of real scenario phishing attacks helps employees understand what the falsified email might look like. And how it can trick them into falling for the scam by offering some incentive or creating a sense of urgency. The test helps the employees in recognizing phishing emails as well as to avoid and report it.
According to phishing statistics 2020, 97% of the users are unable to recognize a sophisticated phishing email. This is probably why phishing attacks, Business Email Compromise (BEC) attacks and other email-based attacks are rapidly increasing every passing year. In fact, BEC attacks yielded the most profit for cybercriminals in 2020!
How to Detect Phishing Attacks?
Phishing attacks today have evolved and become more sophisticated than ever before. These attacks are becoming increasingly difficult to differentiate between a legitimate email and a fake email. But here are a few ways that your organization can follow to detect phishing attacks and protect your organization and the employees against phishing attacks:
It is advisable to always check the name, email address and make sure no alterations (additional letters or numbers) have been made in the email domain or the email address. For example, a legitimate email address might be john@business.com but an altered email address can be john@busineess.com or john@busiiness.com. If you are receiving an email from an unknown organization then you can also check the organization’s domain name by writing the company’s name in a search engine like google.
- Sensitive information and sense of urgency
A legitimate company or any government agency would never ask you to send your sensitive information over email. So, if an organization is asking you to send your credentials or personal information like username or password through email, it is recommended to not send it and get the mail verified personally. Moreover, most of the time scammers create a sense of urgency. Just because if there is not much time left then you don’t have enough time to think or cross-check. But you do not want to be in a hurry when it comes to losing your personal information.
- Poor spellings and grammatical errors
You can often spot a phishing email if it contains poor spelling and grammar errors in the message. Legitimate companies have qualified and trained employees to write emails and the emails are double-checked before the emails are sent out to their staff or clients. So, if a message has poor spelling or grammar errors, it’s always better to cross-check if the email is from a legitimate company.
- Too good to be true or designed to make you panic
It is common for phishing emails to offer a coupon for free stuff or to instill panic. The email message will either be offering some rewards which you were not expecting or will create panic by claiming that your account is compromised. To receive the reward or to secure your compromised account, you will need to verify you are the legitimate person by either giving out your credentials or by entering your login details. The common goal of both messages is to get your credentials or personal information.
- Suspicious links or attachments
Phishing emails come in many different forms but no matter how the email is delivered to you, it always comes with a gateway. It can either be a link to redirect you to a bogus website or an attachment that you are asked to download. No legit companies will randomly send you links or attachments and if they want you to download something then it will be from the official website.
How to Prevent Phishing Attacks?
Your email spam filters might help you keep away numbers of phishing emails from landing into your inox but malicious actors are constantly finding ways to outsmart spam filters. So, it is highly recommended to add extra layers of protection against phishing attacks. Here are some precautious steps your organization can implement:

- Protect the devices by keeping the software up to date with the latest security updates and patches.
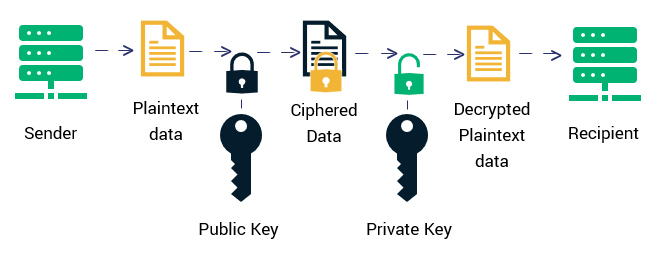
- Enforce strong password policy, passwords that are not easily guessed and avoid sharing passwords to elude the risks of password sharing at work.
- Add an extra layer of security for the password with multi-factor authentication.
- Encourage your employees to report suspicious emails with tools like Threat Alert Button.
- Routine backup the confidential or important data in an external hard drive or cloud storage and also encrypt all sensitive company information.
There are multiple steps your organization can take to prevent email phishing attacks, however, it is important that your employees recognize the phishing emails.
Your organization must get a regular VAPT service in order to identify cybersecurity vulnerabilities and threats. It is a must to implement tools like KDMARC to prevent your email domain against domain forgery and protect your brand.
These services and tools help your organization in safeguarding against cyberattacks and it is highly recommended that you continue. But all it takes is one untrained employee to be tricked by a phishing attack to give away all the information.
The most effective way to educate employees is to provide cybersecurity training with tools to make them aware of the latest cyberattacks including phishing. It will not only provide them with the knowledge of most of the common cyberattacks happening worldwide but will also help them to avoid them.
You can also provide security awareness email samples and phishing awareness emails to employees. It can be done regularly or periodically but to remind them of how it looks and what they should look out for.
Making sure your organization and the employees strictly follow the cybersecurity protocols is the best way. In fact, it is the best possible way out to protect your organization against cyber threats.
“You can fool some of the people all of the time, and all of the people some of the time, but you cannot fool all of the people all of the time.” – Abraham Lincoln
The malicious actors have succeeded in fooling the employees to give out personal information. They have even succeeded in jeopardizing an organization’s network and IT infrastructure. But it’s up to you if these threats shouldn’t harm your organization in the present or in the future by taking the right steps!