Why is Email Security Important?
Whether exchanging emails across networks or dumping them in your spam folder, a huge amount of data is sent, received and stored. You may not realize but there are high chances that an unsecured email might have landed in your inbox which can act as a source of data exploitation. Now you wouldn’t want that, would you? That’s why email security is very essential for our daily routine in order to keep a check if any malicious email is accessing our inbox or not. The cybersecurity professionals working in every industry vertical must stay updated with the prevailing attacks possible through emails.

According to ComputerWeekly.com, 82% of organizations claimed to have faced email-based cybersecurity threats in 2018. Whereas, ransomware seems to be the biggest cyber threat in the coming year. The reason being, ransomware attacks that encrypt critical business files and demand for ransom in return are often sent to individuals working in organizations by emails only!
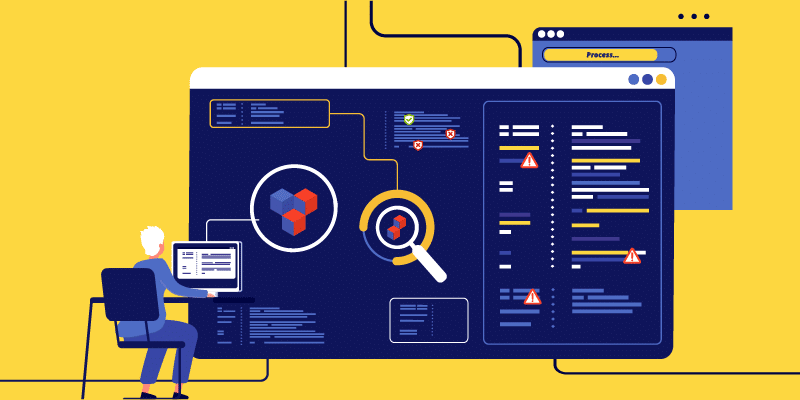
These eye-opening facts call for proper email protection solutions that are needed to be implemented in every organization as a defensive system against invading cyber threats. As far as cybersecurity is concerned, the best solution is using email security tools that incorporate a wide range of security techniques that email accounts and services have. Proceed further for the top 5 email security practices that can benefit your organization from email-based cyber risks.
The 4 Types of Email Security Practices
- Never click the “unsubscribe” link in spam emails:

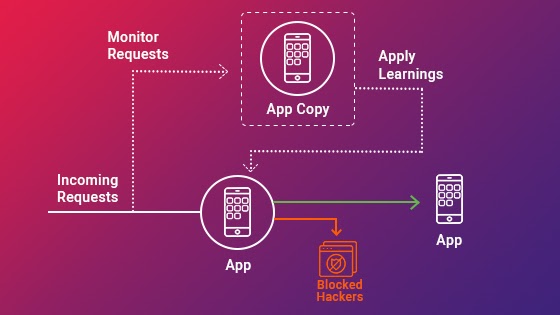
At times, certain emails manage to surpass the spam filter and land in your inbox. For instance, you come across one such certain email and on opening it, you discover that it looks like a phishing email. What would be your first instinct? In any normal situation, users tend to unsubscribe suspicious-looking emails but that is not actually safe!
Hackers are good manipulators and they use such links to fool people into clicking attachment which redirects the targeted users to a phishing site. Apart from that, these links also provide hackers with a back door for access into your system.
-
Avoid Public WiFi:
Never access emails from a public WiFi because they are less secure and hackers choose public WiFi to steal information by passing through a weak network. Cybercriminals require nothing but a laptop and basic software to hack into public WiFi networks and monitor all the traffic. Accessing emails via unsecured public networks can lead to misuse of user’s credentials and a huge loss of sensitive data. This could also result in further intended targeted cyberattacks that are down the line.
-
Email Encryption:
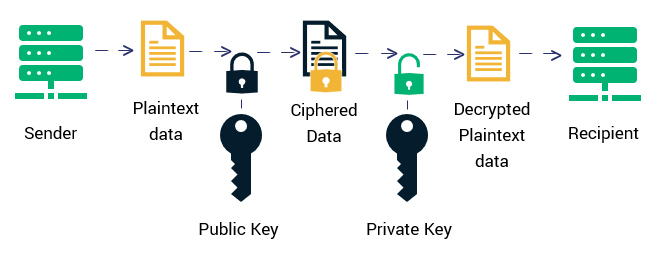
Disguising and encrypting email content potentially protects the sensitive data that is sent and received, from being read by anyone except the intended recipient. With email encryption, you can secure your emails over untrusted networks from eavesdroppers or any third person trying to invade in between the email exchange. This security strategy reduces the chance of disclosure of information as well as alter of message content.
- Employee Education:

Limit the chances of cyber risks in your organization by providing employees with cybersecurity awareness training tools. Along with the implementation of policies and email security tools to prevent cyber threat postures, it is essential to encourage employees to become proactive in combating attack vectors like ransomware, phishing emails, and cyber scams. Security awareness tools is an AI/ML-based security attack simulation tool that assesses the real-time threat posture of an organization. With the unlimited number of attack campaigns and automated training campaigns, this product builds cyber awareness among the employees in an organization and creates a resilient working environment.
Implementing and working on the above-mentioned email protection solutions will not only keep your data safe but will also be beneficial in the long term. In order to protect your business, it is important to make sure that all your employees are empowered to make email based decisions and are protected from data thefts.
Hackers are everywhere nowadays and they won’t stop holding back from discovering vulnerabilities and exploiting your data. Secure your organization now with a robust email security tool in order to reduce the chances of becoming a victim of the prevailing cyber threats.









![A 6-Step Guide to Web Application Testing [Agencies Approved]](https://usersnap.com/blog/wp-content/uploads/2017/05/web-application-testing.png)




















![Possible Best Buy Breach In [24]7.ai Hack | PYMNTS.com](https://www.pymnts.com/wp-content/uploads/2018/04/shutterstock_418940485.jpg)