As mobile applications are emerging as the biggest trend in the market today, it is carrying with it plenty of opportunities for everyone- may it be the developers, the app owners or the users. Mobile apps have created a stir in the market, and therefore, the competition in its market is cutthroat. Therefore, just building a functional and aesthetically pleasing app in no longer enough. Developers must ensure that their app is free from any sort of errors, bugs or glitches which might hinder the UX and avert customers from using it. That’s when TESTING comes into the scene.
Quality Assurance is an indispensable piece of the mobile app development lifespan. Unfortunately, many disregard the basic step of this progression. To guarantee the fruitful development of any application, QA must be engaged with all phases of development, from the ideation stage to breaking down prerequisites, drafting test particulars and deploying the completed item. QA is even the way to post-development audits.
Be that as it may, it can regularly be overwhelming to realise where to begin while making your testing procedure. Mainly follow the below-given steps for a consistent methodology of mobile application testing:
1. Strategizing and Preparation
![How to Prepare for An Effective 2021 Strategic Planning Session [Video]](data:image/svg+xml;base64,PHN2ZyB3aWR0aD0iMSIgaGVpZ2h0PSIxIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciPjwvc3ZnPg==)
This is the first and foremost step after you are done with your development process. This phase requires you to set up a strategy and draft a work plan to define what success means for your app and what constraints it might face. This is a crucial phase as it sets the trajectory for the rest of the steps. The activities that are carried out in this stage are as follows:
- Affinity for different systems
- Check and rundown the necessities:
- Check Frequency of data-usage
- Check Frequency of space-usage
- Dissect practical prerequisites
- Does the application interface with different applications?
- Identify the targeted devices
- Is the application testing constrained to front-end? Does it incorporate back-end testing also?
- Load Handling
- The utility of each feature
- Will the app be Native, PWA, or Hybrid?
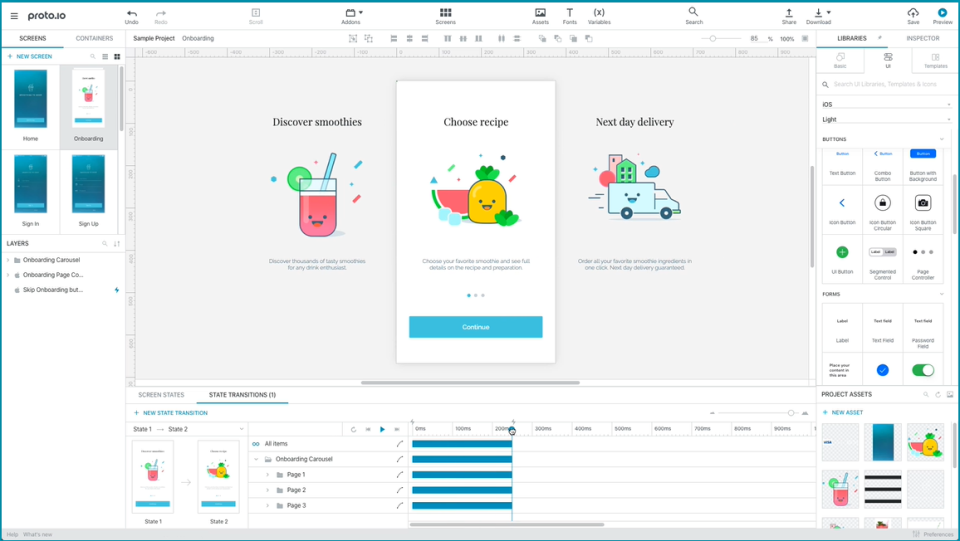
2. Categorise the type of testing required

It is a compulsory necessity that the application needs to work in all iOS and Android gadgets as the end-users can have a variety of gadgets. To guarantee that the application works in every one of the gadgets, we chose a mix of manual testing, automated testing and testing in cloud simulator. This comprises of practical, ease of use, similarity, execution, or security testing on the objective gadgets. Likewise, figure out what sort of practical prerequisites ought to be tried.
3. Test Case and Script Design

The test case is a succession of steps that assist us in executing a specific test on the application. The test script, too, is something very similar. The only difference between these two is that the term test case is used during manual testing, whereas the term test script is used during automated testing. It is very crucial to draft a test case for each and every feature and functionality that you have provided in your mobile application. In addition to that, some extra test cases must also be included.
4. Setup Appropriate Environment for Testing

A testing environment refers to an arrangement of code as well as devices for the testers or automated scripts to perform test cases. In short, it assists in testing with hardware, software, and system designed. Testbed or test environment is arranged according to the need of the App-Under-Test. On a couple of events, testbed could be the mix of the test environment and the test information it works on. Setting up the correct test environment guarantees successful mobile app testing. Any imperfections in this process can lead to additional expense and time of the customer.
5. Manual and Automated Testing

This progression includes executing manual test cases and mechanised test contents on different gadgets, emulators or test systems. Presently these manual test cases and computerised test contents are run on the key functionalities of the application to guarantee that there are no glitches. Record the flaws recognised in the error management system and follow the work plan as devised in the first step.
6. Beta Testing

Beta testing is a significant piece of the application dispatch process. After engineers test their application (that is a thorough testing process called alpha testing), they push it forward to genuine clients to test it. Now, they have the chance to get large blemishes settled before making the application accessible for the more extensive audience. What will the beta testers do? They reliably utilize the application over a particular timeframe. They report back any bugs or issues, and they give their reviews about the application. This aides application distributors to choose whether or not their application is prepared for their target users. On the off chance that it’s not, they’ll have the opportunity to continue improving before it hits the application stores.
7. Performance Testing

Performance testing is the act of assessing how a framework acts as far as responsiveness and soundness under a specific task are concerned. Performance tests are ordinarily executed to analyse speed, power, unwavering quality, and application size. Performance testing assembles each one of the tests that check an application’s speed, strength, unwavering quality, and right estimating. It looks at a few pointers, for example, a program, page and system reaction times, server inquiry handling time, number of acceptable concurrent clients architected, CPU memory utilization, and number/kind of mistakes which might be experienced when utilizing an application.
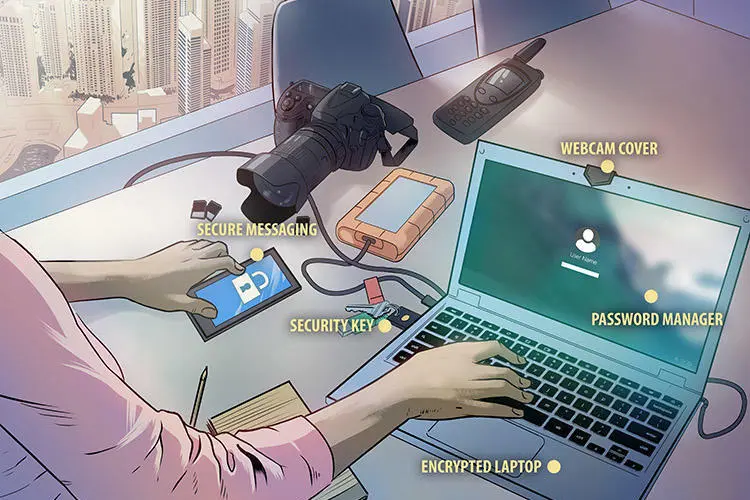
8. Security Testing

Make sure that the application is secure by approving SQL injection, information dumps, session seizing, bundle sniffing, SSL, and gate crashers. Typically, mobile apps have generally less gadget memory and power so it is fundamental that applications must deal with it appropriately. Along these lines, the application performance can be tried by modifying the system from 2G, 3G, 4G to broadband and WIFI. Therefore, the responsiveness, adaptability, and strength are tried in performance testing of an application.
9. Device Testing

Device testing includes a lot of exercises from analysing and rectifying errors, content and administrations on genuine handsets. Testing incorporates confirmation and approval of equipment gadgets and programming applications. During this step, the mobile application is tested on various operating systems as well as a variety of devices so as to ensure that the apps work well when it is launched in the market among the end-users identified with the cloud. The primary motive of this phase is to attain decent test coverage relating to various devices, operating systems or versions of OS.
10. Reporting

At last, the QA administrator produces the test synopsis report. This is an administration report which gives subtleties of any significant data revealed by the tests led, incorporates evaluations of the nature of the testing exertion, the nature of the product framework under test and measurements got from occurrence reports. The report additionally records various kinds of testing performed and the completion of the testing. This assists in improving any future test arranging. This final report shows whether the product framework under test is fit for use and has met acceptance criteria characterized by venture partners.
In a mobile app development venture, mistakes can show up in any of the phases of the development cycle, some of them even stay hidden. Mobile application Testing empowers undertakings to assemble applications that are adaptable and accessible over various stages. It’s a procedure to fabricate a mobile application by testing it for its usefulness, ease of use, and consistency. This is possible via both automation as well as manual testing. Mobile applications are getting more and more complicated with time and there is a requirement for a start-to-end testing. Right from whether the app is downloadable easily, works smoothly, and gives the same kind of experience across various devices. Therefore, we hope that this article has given you enough insights into the mobile application testing process and may come handy when you need it.



















![How to Prepare for An Effective 2021 Strategic Planning Session [Video]](https://www.rhythmsystems.com/hubfs/16_RS_For_Blogs/iStock-862176540.jpg)















/cdn.vox-cdn.com/uploads/chorus_image/image/65619994/Coediting.0.png)