
Blockchain consensus is a decentralized distributed network that offers higher transparency, security, and immutability.
We all know that.
But, have you ever wondered how it is able to achieve all this?
Who governs this network and verifies every transaction, provided there is no centralized authority?
Well it’s Blockchain consensus algorithms – The core part of Blockchain development world that we will be talking about in this comprehensive guide.
TABLE OF CONTENTS:
- Definition of Blockchain Consensus Algorithm
- Objectives of a Consensus Mechanism
- Properties of a Good Blockchain Consensus Mechanism
- Consequences of Relying Upon a Bad Consensus Protocol
- Blockchain Consensus Algorithms that are Popular in the Market
- Proof of Work (PoW)
- Proof of Stake (PoS) and Its Variations
- Byzantine Fault Tolerance (BFT) and Its Derivatives
- Direct Acyclic Graph (DAG)
- Proof of Capacity (PoC)
- Proof of Burn (PoB)
- Proof of Identity (PoI)
- Proof of Activity (PoA)
- Proof of Elapsed Time (PoET)
- Proof of Importance (PoI)
What is Blockchain Consensus Algorithm?

The simplest answer to what is Blockchain consensus algorithm is that it is a procedure via which all the peers of a Blockchain network reaches to a common acceptance or consensus about the real-time state of the distributed ledger.
A consensus mechanism enables the blockchain network to attain reliability and build a level of trust between different nodes, while ensuring security in the environment. This is the reason why it is one of the vital parts of every Blockchain app development guide and every dApp project in the distributed ledger environment.
These algorithms operate on the ground of different objectives, a few of which we will be covering in the next section of this article.
Objectives of Blockchain Consensus Mechanism
1. Unified Agreement

One of the prime objectives of consensus mechanisms is attaining unified agreement.
Unlike centralized systems where having a trust on the authority is necessary, users can operate even without building trustin on each other in a decentralized manner. The protocols embedded in the Distributed blockchain network ensures that the data involved in the process is true and accurate, and the status of the public ledger is up-to-date.
2. Align Economic Incentive

When it comes to building a trustless system that regulates on its own, aligning the interests of participants in the network is a must.
A blockchain consensus protocol, in this situation, offers rewards for good behavior and punish the bad actors. This way, it ensures regulating economic incentive too.
3. Fair & Equitable

Consensus mechanisms enable anyone to participate in the network and using the same basics. This way, it justifies the open-source and decentralization property of the blockchain system.
4. Prevent Double Spending

Consensus mechanisms works on the basis of certain algorithms that ensures that only those transactions are included in the public transparent ledger which are verified and valid. This solves the traditional problem of double-spending, i.e, the problem of spending a digital currency twice.
5. Fault Tolerant
Another characteristic of Consensus method is that it ensures that the blockchain is fault-tolerant, consistent, and reliable. That means, the governed system would work indefinite times even in the case of failures and threats.
Currently, there are a plethora of Blockchain consensus algorithms in the ecosystem and many more are heading to enter the marketplace. This makes it imperative for every Blockchain development company and enthusiastic Entrepreneur to be familiar with the factors that defines a good consensus protocol, and the possible effect of going with a poor one.
So, let’s begin with determining what makes a Blockchain consensus a good one.
Properties of a Good Blockchain Consensus Mechanism

1. Safety
In a good consensus mechanism, all the nodes are capable of generating results that are valid according to the rules of protocol.
2. Inclusive
A good consensus mechanism ensures that every particular node of the network participates in the process of voting.
3. Participatory
A consensus mechanism where all the nodes actively participate and contribute to updating database on Blockchain is called a Good consensus model.
4. Egalitarian
Another trait of a good mechanism is that it gives equal value and weightage to every vote received from the node.
With this attended to, let’s find out what happens when you do not consider these factors and introduce a poor consensus model to your development process.
Consequences of Choosing a Bad Consensus Protocol
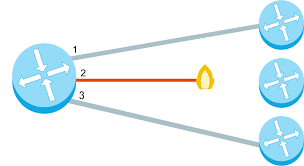
1. Blockchain Forks
Choosing a poor blockchain consensus method increases the vulnerability of the chain. One such vulnerability that is faced by the blockchain enthusiasts and developers is Blockchain Forks.
Blockchain forks, in a layman language, is a situation or circumstances under which a single chain diverges into two or more. A detailed explanation about Blockchain fork and its types is available in the video embedded below.
When a Blockchain fork occurs, the application begins operating in an unpredictable manner, creating two or more diverged nodes ahead.
2. Poor Performance

When a bad consensus mechanism is considered, either the node gets malfunctioned or suffer from network partition. This delays the process of exchanging messages between nodes and increases the latency of the application, which ultimately lowers down the performance level.
3. Consensus Failure

Another effect of incorporating a bad consensus mechanism to your business model is consensus failure. In this situation, a fraction of nodes fails to participate in any process and thus, in the absence of their votes, the consensus fails to deliver accurate and desired outcomes.
With the basics of Blockchain consensus methods now covered, let’s dive deeper into the topic and look at the popular types of consensus mechanism.
Blockchain Consensus Algorithms that are Popular in the Market
1. Proof of Work (PoW)
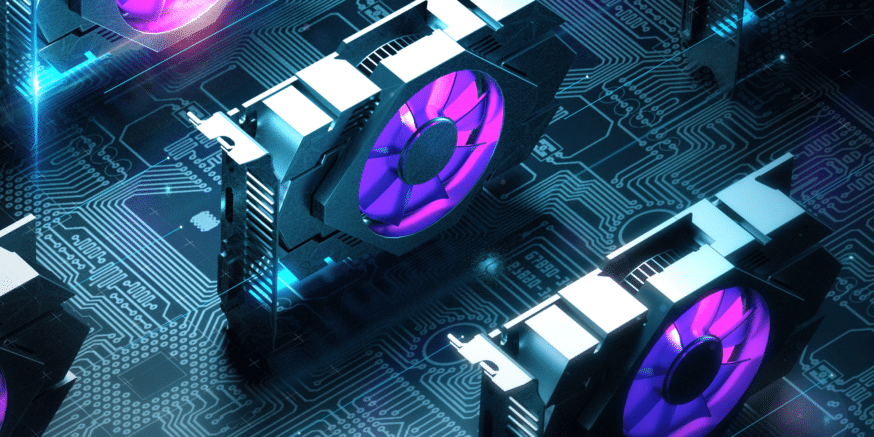
Developed by Satoshi Nakamoto, Proof of Work is the oldest consensus mechanism used in the Blockchain domain. It is also known as mining where the participating nodes are called miners.
In this mechanism, the miners have to solve complex mathematical puzzles using comprehensive computation power. They use different forms of mining methods, such as GPU mining, CPU mining, ASIC mining, and FPGA mining. And the one that solves the problem at the earliest gets a block as a reward.
However, the process is not that easy. A puzzle can be solved only via trial and error method. Additionally, the level of complexity of the puzzle increases with the speed at which blocks are mined. So, it becomes mandatory for one to create a new block within a certain time frame to cope up with the difficulty level.
The Proof of Work mechanism is used by multiple cryptocurrencies like Bitcoin, Litecoin, ZCash, Primecoin, Monero, and Vertcoin to name a few.
In terms of its implementations, the Proof of Work (PoW) has not only influenced the financial industry, but also healthcare, governance, management and more. It has, in fact, offered the opportunity of multichannel payments and multi-signature transaction over an address for enhancing security.
2. Proof of Stake (PoS)

Proof of Stake is the most basic and environmentally-friendly alternative of PoW consensus protocol.
In this blockchain method, the block producers are not miners, but they act like validators. They get the opportunity to create a block over everyone which saves energy and reduces the time. However, for them to become a validator, they are supposed to invest some amount of money or stake.
Also, unlike that in the case of PoW, miners are provided with a privilege to take their transaction fees in this algorithm for there is no reward system in this consensus model.
This, as a whole, encouraged brands like Ethereum to upgrade their model from PoW to PoS in their Ethereum 2.0 update. Also, it helped various Blockchain ecosystem like Dash, Peercoin, Decred, Reddcoin, and PivX to function properly.
Now, while PoS solved various issues earlier associated with PoW, there were many challenges still undusted in the market. To mitigate those challenges and deliver an enhanced blockchain environment, several variations of PoS came into existence.
The two popular variations of Proof of Stake (PoS) are DPoS and LPoS.
- Delegated Proof of Stake (DPoS)
In the case of Delegated Proof of Stake (DPoS), the participants stake their coin and vote for a certain number of delegates such that the more they invest, the more weightage they receive. For example: if user A spends 10 coins for a delegate and user B invests 5 coins, A’s vote gets more weightage than that of B.
The delegates also get rewarded in the form of transaction fees or certain amount of coins.
Because of this stake-weighted voting mechanism, DPoS is one of the fastest blockchain consensus models and highly preferred as a digital democracy. Some of the real-life use cases of this blockchain consensus mechanism are Steem, EOS, and BitShares.
- Leased Proof of Stake (LPoS)
LPoS is an enhanced version of PoS consensus mechanism that operates on the Waves platform.
Unlike the regular Proof-of-Stake method where each node with some amount of cryptocurrency is entitled to add the next blockchain, users can lease their balance to full nodes in this consensus algorithm. And the one that leases the bigger amount to the full node have a higher probability of generating the next block. Also, the leaser is then rewarded with a percentage of transaction fee that has been collected by the complete node.
This PoS variant is an efficient and safe option for the development of public cryptocurrencies.
3. Byzantine Fault Tolerance (BFT)

Byzantine Fault Tolerance, as the name suggests, is used to deal with Byzantine fault (also called Byzantine Generals Problem) – a situation where the system’s actors have to agree on an effective strategy so as to circumvent catastrophic failure of the system, but some of them are dubious.
Learn more about the Byzantine Generals Problem through this video:-
The two variations of BFT consensus model that are prime in the Blockchain arena are PBFT and DBFT.
- Practical Byzantine Fault Tolerance (PBFT)
PBFT is a lightweight algorithm that solves the Byzantine General’s problems by letting users confirm the messages that have been delivered to them by performing a computation to evaluate the decision about the message’s validity.
The party then announces its decision to other nodes who ultimately process a decision over it. This way, the final decision relies upon the decisions retrieved from the other nodes.
Stellar, Ripple, and Hyperledger Fabric are some of use cases of this blockchain consensus mechanism.
- Delegated Byzantine Fault Tolerance (DBFT)
Introduced by NEO, the Delegated Byzantine Fault Tolerance mechanism is similar to DPoS consensus model. Here also, the NEO token holders get the opportunity to vote for the delegates.
However, this is independent of the amount of currency they invest. Anyone who fulfills the basic requirements, i.e, a verified identity, right equipment, and 1,000 GAS, can become a delegate. One among those delegates is then chosen as speaker randomly.
The speaker creates a new block from the transaction that is waiting to be validated. Also, he sends a proposal to the voted delegates who have the responsibility to supervise all the transactions and record them on the network. These delegates have the freedom to share and analyze the proposals to check the accuracy of data and honesty of the speaker. If, then, 2/3rd of the delegates validates it, the block is added to the blockchain.
This type of Blockchain consensus protocol is also called ‘Ethereum of China’ and can be a helpful resource in building a ‘smart economy’ by digitising assets and offering smart contracts on the blockchain.
4. Direct Acyclic Graph (DAG)

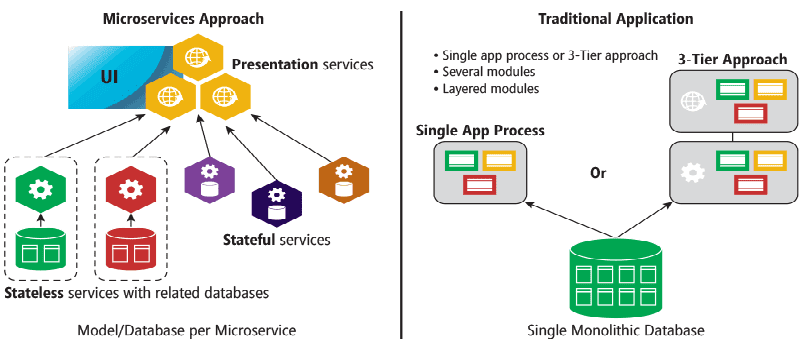
Another basic yet prime blockchain consensus model that every mobile app development services company working with Blockchain must be familiar with is DAG.
In this type of Blockchain consensus protocol, every node itself prepares to become the ‘miners’. Now, when miners are eradicated and transactions are validated by users itself, the associated fee reduces to zero. It becomes easier to validate transactions between any two closest nodes, which makes the whole process lightweight, faster, and secure.
The two best examples of DAG algorithm are IOTA and Hedera Hashgraph.
Though these are the prime consensus models in the development environment, many different blockchain consensus mechanisms have slowly and gradually starting gaining momentum, such as:-
5. Proof of Capacity (PoC)

In the Proof of Capacity (PoC) mechanism, solutions for every complex mathematical puzzle is accumulated in digital storages like Hard disks. Users can use these hard disks to produce blocks, in a way that those who are fastest in evaluating the solutions get better chances for creating blocks.
The process it follows is called Plotting. The two cryptocurrencies that relies on PoC blockchain consensus protocol are Burstcoin and SpaceMint.
6. Proof of Burn (PoB)

Considered an alternate solution to PoW and PoS in terms of energy consumption, Proof of Burn (PoB) consensus model works on the principle of letting miners ‘burn’ or ‘ruin’ the virtual cryptocurrency tokens, which further provides them with a privilege to write blocks in proportion to the coins. The more coins they burn, the more are the chances of picking the new block for every coin they get.
But, in order to burn coins, they are required to send it to the address where it couldn’t be spent for verifying the block.
This is widely employed in the case of distributed consensus. And the finest example of this consensus mechanism is the Slim coin.
7. Proof of Identity (PoI)

The concept of PoI (Proof of Identity) is just like that of the authorized identity. It is a piece of cryptographic confirmation for a users’ private key that is being attached to each particular transaction. Each identified user can create and manage a block of data that can be presented to others in the network.
This blockchain consensus model ensures authenticity and integrity of the created data. And thus, is a good choice for introducing in smart cities.
8. Proof of Activity (PoA)

PoA is basically a hybrid approach designed through the convergence of PoW and PoS blockchain consensus models.
In the case of PoA mechanism, miners race to solve a cryptographic puzzle at the earliest using special hardware and electric energy, just like in PoW. However, the blocks they come across holds only the information about the identity of block winner and reward transaction. This is where the mechanism switches to PoS.
The validators (shareholders appointed to validate transactions) test and ensure the correctness of the block. If the block was checked many times, the validators activate to a complete block. This confirms that open transactions are processes and are finally integrated into the found block containers.
Besides, the block reward is divided so that validators gain shares of it.
The two real-world implementation of this mechanism are Espers and Decred coins.
9. Proof of Elapsed Time (PoET)

PoET was introduced by Intel with an intent to take over cryptographic puzzles involved in PoW mechanism by considering the fact that the CPU architecture and the quantity of mining hardware knows when and at what frequency does a miner win the block.
It is based on the idea of fairly distributing and expanding the odds for a bigger fraction of participants. And so, every participating node is asked to wait for a particular time to participate in the next mining process. The member with the shortest hold-up time is asked to offer a block.
At the same time, every node also come up with their own waiting time, after which they go into sleep mode.
So, as soon as a node gets active and a block is available, that node is considered as the ‘lucky winner’. This node can then spread the information throughout the network, while maintaining the property of decentralization and receiving the reward.
10. Proof of Importance (PoI)

Introduced by NEM, PoI is a variation of PoS protocol that considers the role of shareholders and validators for its operation. However, this is not only influenced by the size and chance of their shares; various other factors like reputation, overall balance, and no. of transactions made through any particular address also plays a role in it.
The networks based on POI consensus model are expensive to attack on and rewards users for contributing to the network’s security.
The information shared so far would have helped you in differentiating the varied Blockchain consensus protocols.
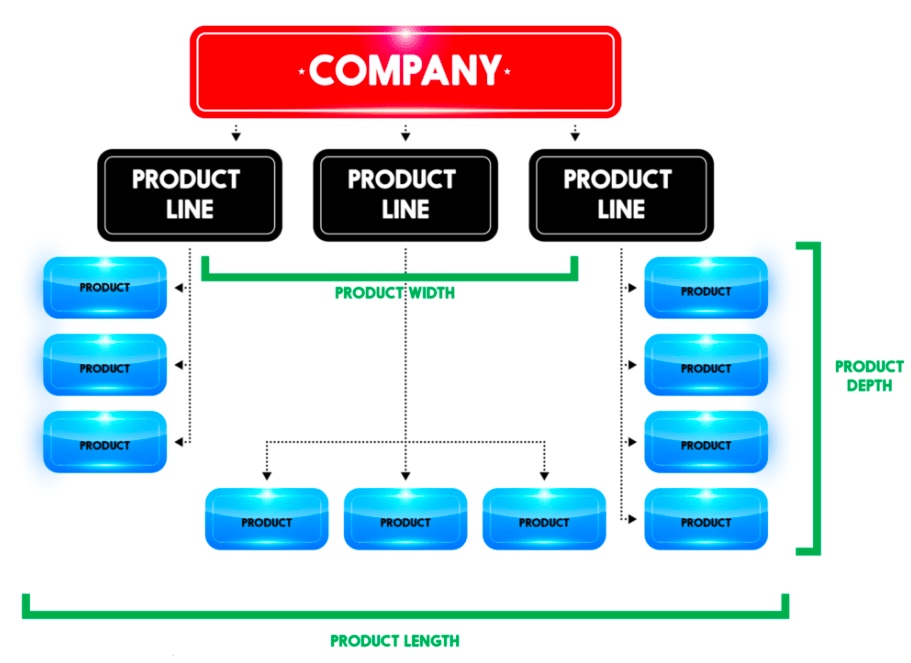
However, to simplify it for you, here’s a blockchain consensus algorithms comparison table.












:max_bytes(150000):strip_icc()/GettyImages-625727674-5a6d3a236b974564a4e39795bfcbd827.jpg)




























/GettyImages-895702720-5b2e41603e1d4c7786023f4ffa54192f.jpg)







![Part 2]: Digital Transformation in Manufacturing: Defining the Digital Transformation Strategy and The Challenges Ahead | by PlumLogix (Salesforce Partner) | PlumLogix | Medium](https://miro.medium.com/max/718/1*9tUukbhz-A85Omxv0NbZFg.jpeg)





