
For the past few years, many variations of fintech trends have emerged with the implementation of cutting-edge technologies and tools. Various fintech subdomains have come into the limelight, while many banks and startups have realized the effects of fintech on businesses and changed their traditional processes.
However, this is just the beginning of a revolution.
In the 8 months lying ahead of us, many fintech trends are expected to come into the limelight. Numerous standardization and regulations are anticipated to immerse the fintech industry with new enjoyment and excitement, and make the market worth $309.98 Bn by the end of 2022.
Wondering what are these top fintech trends for 2020?
How will these trends revolutionize the future of fintech?
Let’s catch up here quickly.
20+ Fintech trends you must act on in 2020
1. Focus on unserved and underserved

According to a report by the World Bank, around 1.7 Bn people are not a part of any formal financial system. They do not have any bank account of their own, a few reasons behind which are:-
- 60% of people do not have enough money,
- 30% of people never felt the need of a bank, and
- 26% of people find accounts as an expensive affair.
This is the foremost area where the fintech leaders are focusing this year. Rather than entering the established market, the fintech startups are trying to enter new phases and win financial backing from investors this year. They are seeking innovative ways to communicate with people from different walks of life, understand their financial challenges, and come up with better funding opportunities to ultimately drive customer loyalty and profits.
A clear evidence of which is Uber.
On discovering that around 60% of their drivers lay constraints on their banking accounts 6 times a month, and send 25% of their earnings to their native countries while suffering from high fees, the company launched its fintech division – Uber Money. This enables the targeted audience, i.e, drivers and other freelancers to get real-time income, save a big share of each trip, and get better functionalities of bank account, debit card, and mobile banking application.
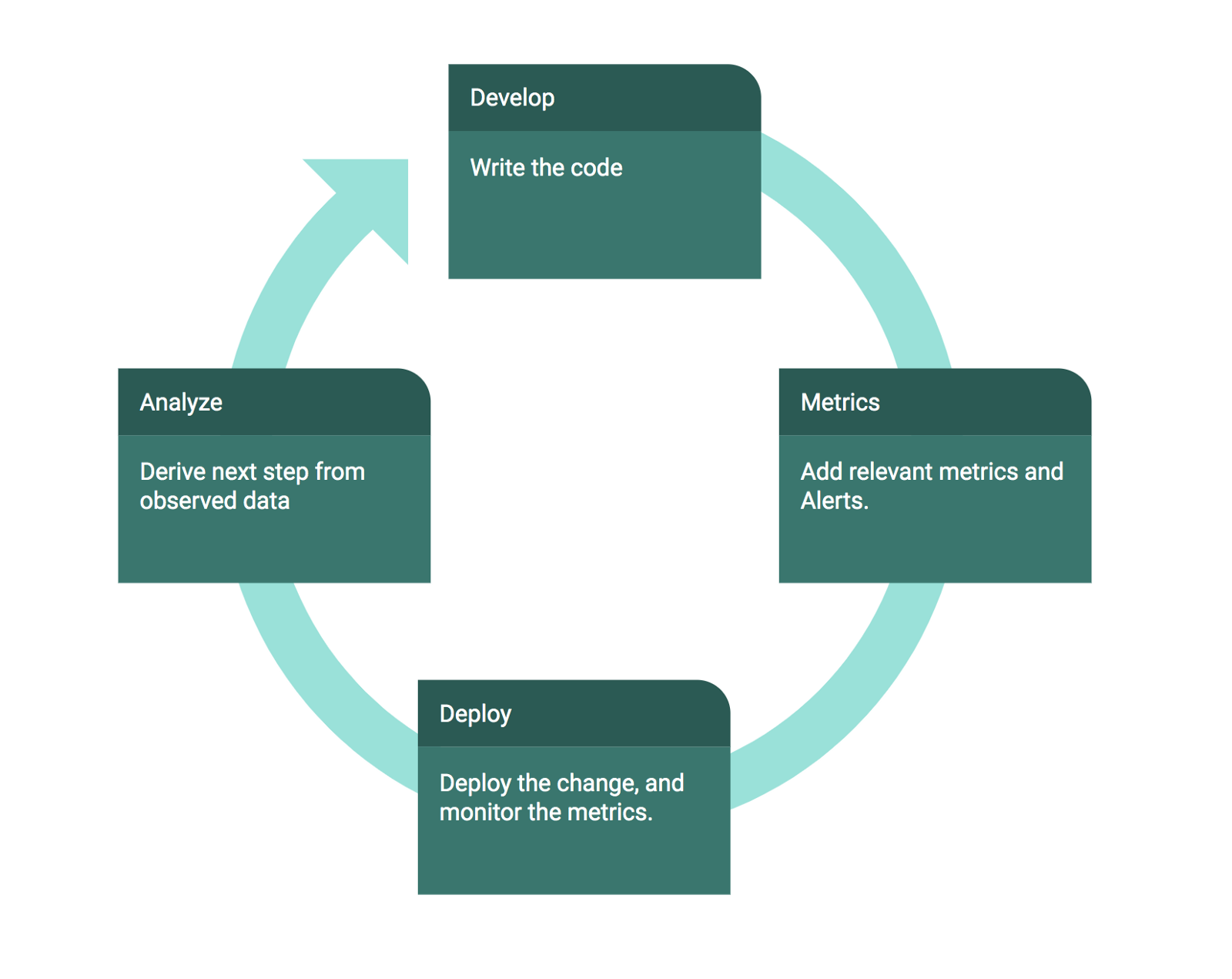
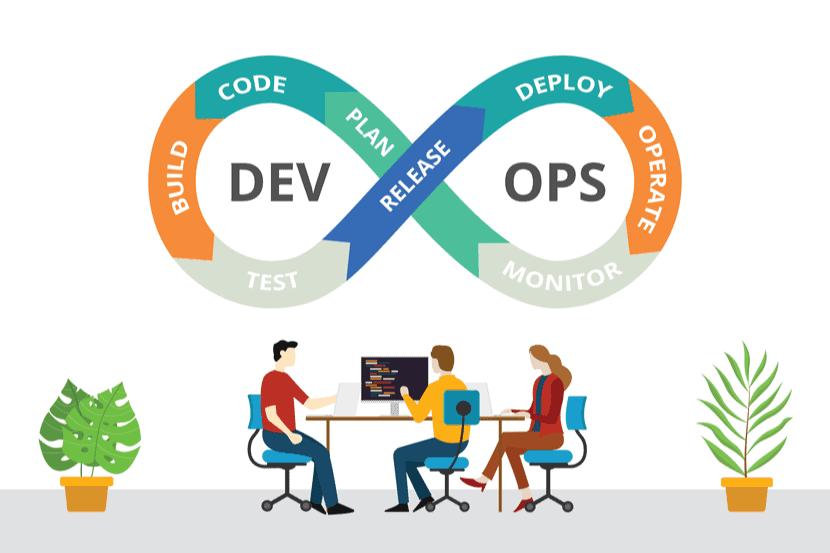
2. Automation and RPA

Robotic Process Automation (RPA) is also one of the trends that will revamp the fintech ecosystem in 2020.
These bots will not solely continue to automate human repetitive processes, but also lower down common errors and inefficiencies, which will ultimately enhance productivity and ROI.
3. Reduced use of physical money

Another trend that will indicate higher use of finance technological services is decline in the use of physical money.
In 2016, only 1% of the transactions made in Sweden were using cash – a prime reason of which is that many businesses denied accepting cash payments. Likewise, the United Kingdom recorded the highest volume of cashless payments, i.e, of €10.67 Bn in 2017. And now, in the year 2020, this value will accelerate with the usage of more convenient solutions like contactless payments via NFC.
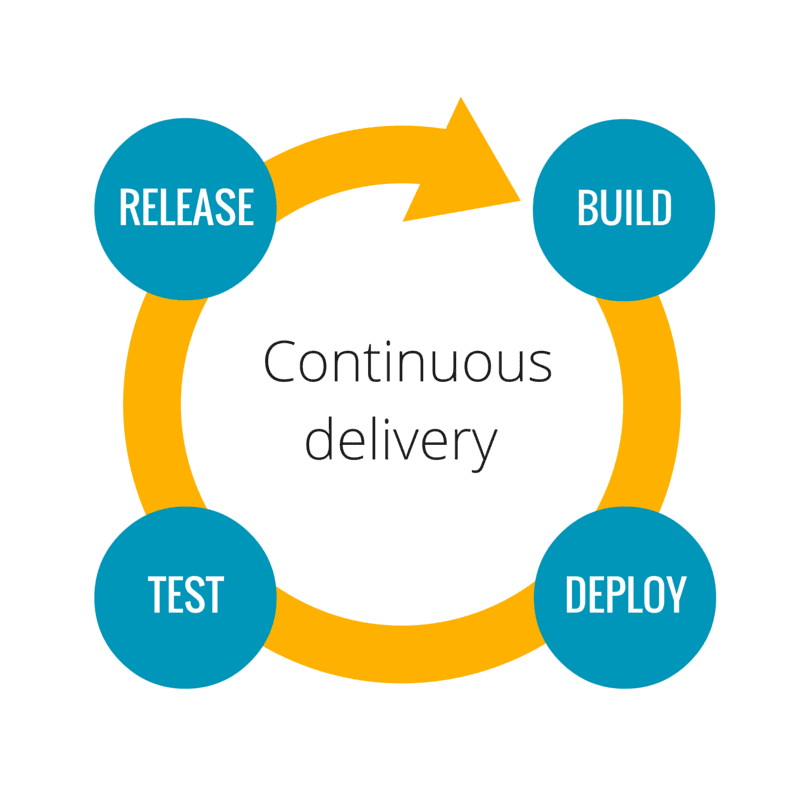
4. Continual development of Open Banking

One of the top banking and fintech trends for 2020 and beyond has to be Open banking. It leverages APIs that allow third-party developers to develop apps and services around the financial institution, in order to help users enjoy the online banking service via multiple platforms.
According to a Deloitte study, around 22% of banks have already deployed their own API platforms, while 39% are working on it. And many more are anticipated to enter this sector.
5. Implementation of Voice-Search

The fact that by 2020, almost 50% of all searches will be voice-based on the Internet, is enough to give you a hint of the future of fintech and the role it is playing in transforming the banking and finance sector. Voice-based search in banking software will assist customers in easily accessing banking services, provide ways of encryption while supporting communication with NLP-powered voice assistants.
More and more industries and banking institutions are adopting voice search- one of the latest technologies used in fintech, and why wouldn’t they when it can save up to $3 billion.
6. Decentralized Finance

Decentralized Finance (DeFi) is also one of the emerging trends in the finance industry.
In 2020, companies will rely upon different set of technologies such as distributed ledger technology (record-keeping decentralization), Internet of Things (IoT), Big data, online P2P systems (risk-taking and decision-making decentralization), and Edge computing to offer monetary interactions in a more decentralized manner.
This fintech trend has already been transforming the payment and settlements. And, in the coming years, it will also change the way capital markets, lending, and trade finance operates while ensuring advantages like enhanced speed, lower cost, and higher transparency.
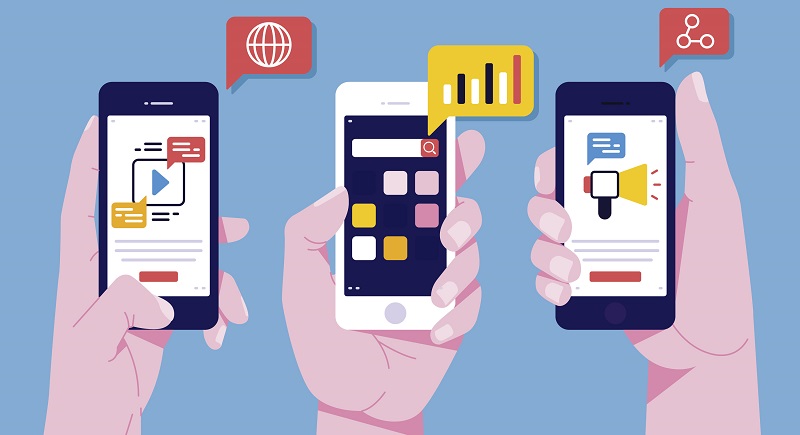
7. Upsurge in mobile apps usage

Not as surprising as others, mobile apps are also gaining popularity in the fintech industry and have proved potent for becoming a trend. With the incessantly growing popularity of mobile apps, many fintech companies have started to tie up with the best banking & finance app development company in order to create impeccable digital solutions. There are all kinds of innovations waiting around the corner which we will see throughout this year.
8. Next-gen digital-only banks

A rapid increase has been witnessed in partnerships among Fintech companies and banking institutions, promoting the emergence of new financial intermediaries. Now, Digital-only banks are gaining unprecedented popularity, something that was not anticipated in this decade at least.
With an additional time economy option, these Digital-only banks offer an even more diverse array of services to their customers. No wonder, Digital-only banking is going to be one of the top fintech trends for the year, because of its connection with disrupting technology like Blockchain and cryptocurrency.
9. Improvement in Conversational banking

According to a study by Accenture around CUI (conversational user interfaces), it has been found that –
- 64% of people prefer interacting via messages or emails over calling,
- 64% users are more likely to buy or hire a service if they have chatted with the brand earlier too.
Because of this, banks and fintech organizations will emphasize more on conversational banking. They will come up with AI-based chatbots and other software that interacts with users on different messaging platforms like Facebook messenger and WhatsApp.
10. Higher downloads of Digital wallets

Digital Wallets are effectively on a way to eradicate fiat money from the wallets. In fact, in a report by Grand View Research, it was revealed that the digital wallet market size was valued to be USD 16.65 Bn in 2013 and is predicted to reach USD 7,581.91 Bn by 2024.
Alone in 2018, the number of digital-wallet users was 440 Mn and has surely increased in 2019 and will continue to do so in 2020. To support this statement, look at the graph below depicting the rise in wallet users.
11. Application of AI and ML-powered chatbots and automated customer services

A generally accepted statement – AI is our past, present, and future clearly shows how humongous this technology is going to be, changing the face of every industry, including Finance and banking.
As per AI technology trends, the market size of AI in the Fintech market is predicted to increase from $959.3 Mn in 2016 to $7305.6 Mn by 2022, at a CAGR of 40.4%.
The technology, this year, is going to provide better services to everyone in the form of –
These are increasingly becoming a choice of financial institutions for customer support services. You ask why? Well, these chatbots in fintech domain are available to the customer 24X7 without incurring additional monthly expenses. They leverage the advancements of ML algorithms and NLP (natural language processing) to serve customers in all possible ways.
Another thing is that chatbots are incredible for enhancing customer engagement. Some of the chatbots used by popular banks worldwide are Ceba (Commonwealth Bank Australia), Erica (Bank of America), and Eva (HDFC Bank).
AI-based customer intelligence is something financial bodies are gaining more and more interest in. It is because customer intelligence helps these institutions to have a deeper understanding of users through their banking relationships and transactions by analyzing data gathered via technology. Some organizations have already started implementing it in their analysis process while many will follow suit in 2020, making it a notable Fintech trend for 2020.
-
Regulators using AI to predict potential issues
In the year 2020, we may encounter changes in the way regulators perform certain actions. Since AI is prominent as of now, they are bound to turn to AI’s algorithm, data gathering, and analytics tools to compare scenarios and predict probable issues and risks.
12. Introduction of Blockchain in banking and fintech solutions

This year, the role of Blockchain in the fintech sector will reach to the next level. The technology will bring disruptive changes to the fintech industry, making the market valued $6,700.63 Mn by the year 2023.
Many terminologies like the ones described below will go mainstream this year:-
Without a doubt, a boon for the finance industry, Smart contracts (a decentralized financial technology) are quickly gaining popularity. They are an evolution of pen and paper contracts – more effective, more secure, and of course, immutable.
Wonder how they work?
Let’s take an example-
In smart contracts, parties sign smart contact by using cryptographic keys (digital signature as you will). Now, instead of using pen and paper, the contracts are encoded in computer language. And these codes are virtually tamper-proof, hence immutable contracts.
-
Crypto-To-Cash Conversions
Cryptocurrencies are becoming more prominent every day and institutional investors are expected to show their interest in cryptocurrency adoption. And this all is a result of new initiatives that have emerged to increase their real-world implications. New advancements may surface in 2020 targeting crypto-to-cash difficulty and may give us what we are looking for.
In fact, many digital-only banks or the banks collaborating with Fintech are already actively considering the possibility of cryptocurrency implementation in order to perform money operations.
13. Incorporation of Big Data in fintech processes

The impact of big data technology on financial services is yet another thing that will be taken into consideration this year.
Big Data is one of the effective tools that fintech market players employ to circumvent the incumbents and revolutionize the industry. On a broader scale, the technology is helping fintech companies grow in numerous ways, including:-
With core focus on users’ convenience, fintech startups divide their target user base on the basis of different factors such as age, gender, location, online behavioral patterns, and economic health to determine their spending habit and build highly-customized and personalized offers and financial products.
Predictive analytics is a robust tool that offers risk management and enables companies to avoid poor debt expense or make better decisions related to crediting. Fintech startups mine data to create risk profiles of consumers applying for financing to detect bad payers or poor investments.
With the help of big data engines, fintech companies will be able to gain a better understanding of the consumers’ buying habits and online patterns which can further help with detecting and forbidding suspicious behavior more accurately and quickly.
14. Advent of Co-browsing

The screen-sharing is generally the function where one party gives access to another party for sharing the device’s screen. With the help of co-browsing, users will be able to prevent others from gaining complete access to the device. Instead, it lets users share a particular web page with another party for mutual access. Something that is a boon for the finance and banking sector, as it is very useful in banking software.
With co-browsing intuition, representatives can easily assist customers with issues pertaining to the completion of bank formalities and documentation, to name a few. This is what makes it one of the banking tech trends for 2020.
15. Disruption of Payroll process

Around 59% of consumers struggle from paycheck to paycheck in the USA alone. This situation has created serious money concerns for many individuals who rely on payday loans or predatory lenders asking upto 400% rates for a two-week credit; making one of the financial technology trends of 2020 and beyond.
With the help of fintech companies, other organizations are improving the traditional ways of payroll. Companies such as Gusto, which has been valued at $3.8 Bn, have introduced a flexible Pay feature that allows employees to pick a date to receive their payroll. Another example at hand is the Earnin app allowing users to get access to their earnings before their scheduled payday.
16. Growth of Asian market

The Asian market is rapidly becoming the biggest adopter of Fintech. As new Fintech companies start to emerge, we can expect great advances in the Asian market.
On analyzing the events of 2019, it was noted that China has emerged to be the global leader in the Fintech industry. With the world’s biggest population, the country has 800 Mn internet users – a combined percentage of countries like Mexico, Japan, Russia, and the US.
17. Enhanced ‘A’ rated life insurance carriers
Another financial service technology for 2020 related to insurance is the ‘A’ rated life insurance carriers. Now, the institutions will employ technology in a way as to eliminate the medical exam while simplifying the writing and underwriting of a new life insurance policy.
Some of the fintech startups are implementing up to $1 million of term coverage without any medical exam and only refer to the data collected on customers regarding the prescription history based on their medical questionnaire for passing approval.
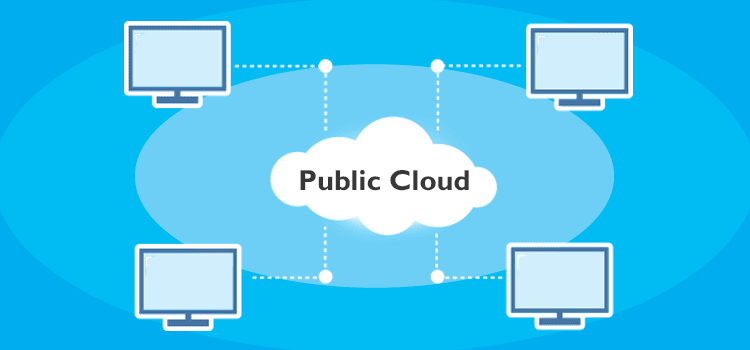
18. Public cloud to be the new infrastructure model

Even now, many financial institutions seek help from cloud-computing for an array of work and processes. They use cloud-based SaaS apps for things that may be deemed non-core like HR, CRM, and accounting. The core service infrastructures in areas including consumer payments, credit scoring, and statements are going to become utilities by 2020.
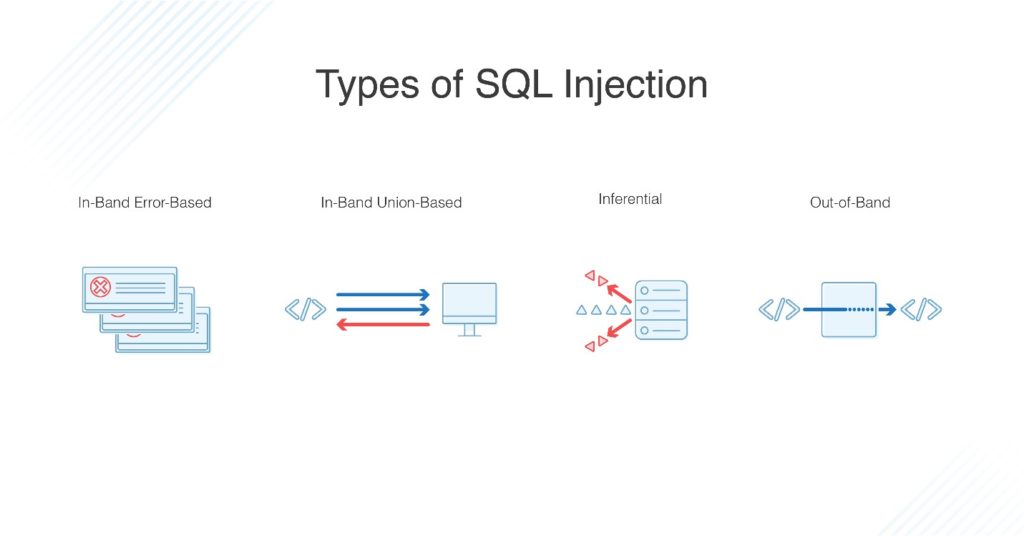
19. Cybersecurity as a pillar of fintech domain

Since everything is online now, there is a rapidly increasing threat of cybercrimes, something which all financial institutions, among others, want to avoid at any cost. In this case, there have been many advancements in this segment developing robust security systems to creating next-gen tools for data protection.
Cyber risk analytics has also merged to be an interesting implementation of AI in Fintech to detect probable threats. With what we have witnessed so far in 2019, it is without a doubt that improving cybersecurity is going to be one of the top Fintech trends in 2020.
20. Rise of Financial regulations and Regtech companies

With consumers having concerns over data sharing with unknown third-party firms, the rise of RegTech firms and financial regulations will also be one of the fintech trends for 2020.
Currently, around 15% of the workforce of the entire financial sector is engaged in tasks around ‘compliances’. But, in the coming years, more regTech solutions will come into the limelight; offering finest services like compliance verifications, transaction monitoring, risk management, ‘Know-Your-Customer’ (KYC) or ‘Anti-Money Laundering’ (AML) practices, and more. And eventually, make the market size grow from $10.6 Bn in 2017 to $53 Bn by the end of 2020.
21. Partnership and collaborations will be on the rise
Partnerships and mergers among fintech companies are going to be one of the top fintech trends for 2020, according to Kathleen Craig, founder, and CEO of HT Mobile Apps (a fintech company). Startups and small organizations are coming to the realization that partnerships are more profitable.
More so, till now direct-to-customer fintech companies have been stuck on a particular piece of the market, but with these mergers, we can see a whole new spectrum of services they together may offer.
22. Sharing economy will become integral
What started with cars, taxis, hotel rooms, etc.will now expand its horizons to include financial services. The sharing economy is expected to become a huge Fintech trend for 2020.
Here, the sharing economy pertains to decentralized asset ownership and the use of IT to obtain suitable matches between providers and users of capital, instead of turning to a bank as an intermediary element.
23. Establishment of On-demand insurance economy

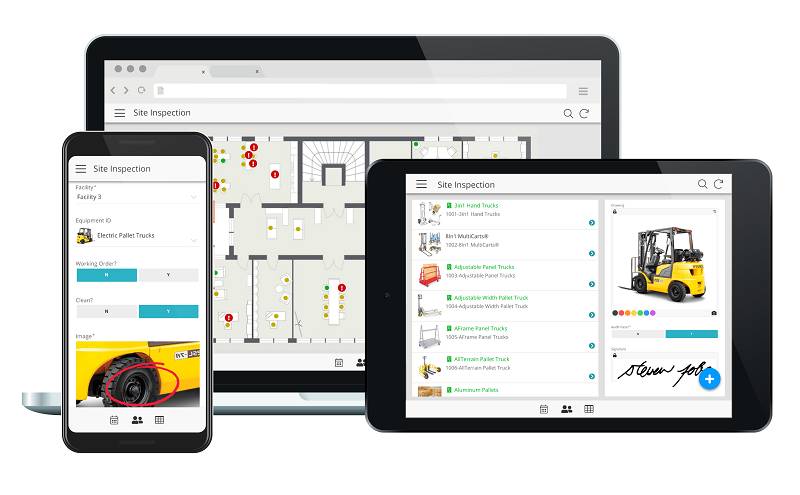
The on-demand model has become one of the most in-trend concepts of this decade and will continue to do so in the coming one. In fact, on-demand mobile app economy statistics are legit proof of its popularity.
Just like you can get a taxi on-demand via apps like Careem and Uber, you can also avail insurance in a matter of minutes. Financial institutions have started to offer insurance facilities via mobile apps. Customers can easily apply insurance for real estate, car, and other belongings, simplifying and making the whole process more efficient.
While these are the trends that are forecasted to change the landscape of the fintech industry between 2020-2025, many more are expected to join the league. In such a scenario, it is advisable to visit this blog again in the future and get familiar with more disrupting fintech trends for 2020 and beyond.





















































![8 Mobile App Retention Strategies For 2021 [With Examples]](https://content.webengage.com/wp-content/uploads/sites/4/2020/03/Retention.ai_2-01-700x300.jpg)












/GettyImages-962574588-d07e325236e84e23971c5f6d5079775e.jpg)






