No one can doubt the popularity and dominance of the Google Play Store in the domain of mobile applications and software.
The domain gets all the more solidified by the Play Store statistics that there are approximately 2.8 million apps on Play Store and that almost 3739 apps get released on it daily.
Numbers like these solidify how Play Store is an excellent option to upload your application on.
Now, if you are wondering “How to submit an app to Google Play Store” then end your quest here. We have covered end-to-end all about the process to upload an app to Google Play Store.
To put it out there, there are certain things that need to be done before the actual process of app submission begins. This is what we are going to attend to before answering the question of “How to get an app on the play store”, we will look at the pre-steps to publishing an application.
Without any further ado, let’s dive in.
Prerequisite of Submitting App To Play Store
Since this is your first time submitting your application to a gigantic platform, there are certain prerequisites that you must take care of in order to successfully upload an app to Google Play Store. So, without any further ado, let’s get started.
1. Test Your Application

It is needless to mention how crucial testing your application is. No matter how many incredible features you have packed into your app, if it does not perform upto the expectations of the user, it will be ditched like a hot potato. In which case, it is imperative for you to painstakingly test your app as many times as possible and be 100 percent certain that it is going to perform remarkably, before you look ahead to upload apps on Play store.
You can always use emulators for this purpose, however, using an Android-powered device will make the testing process more effective. It will give the experience of using your app on a real device, as would users, and enable you to analyze any bugs or discrepancies.
2. Concise App Size

In terms of applications, the size of the app matters a lot. Users do not feel inclined to download an app that takes too much space in their device storage. Moreover, Google only permits the app size to up to 50MB.
Although, if your app exceeds this limit, then you can use Android APK’s Expansion file, to successfully upload the app to Play Store. This will break your app into parts and each can be up to 2GB, giving an additional 4GB space to your app. This added data is saved in Google Cloud and is retrieved whenever the app is installed.
3. Get App Licensed

Though this is an optional choice, it wouldn’t hurt you to get your app licensed before you upload your app to Google Play Store. Licensing your application will prove most beneficial for you if it is paid in nature. By adding the End User License Agreement, you will gain full control over your application which may help in the future, should any discrepancies arise.
- Create your APK file with Bundle ID and Version Number
- You need to prepare an APK file in which you can assign a version number to your application which will help you in the future when you need to upload a new update for your app. This number is mentioned in the code and would increase as the updates for the application are introduced.
- Bundle ID, also called App ID, is used to make an application unique, making it a crucial part of the prerequisites for submitting your application. This is applicable for all the applications for Android 5.0 and above.
4. Sign App With Security Certificate

Here, you need to create a private key using Release Keystore. This is a security certificate signed as an APK which you will need every time you publish an app to the Play Store. This is also known as JSK file including credentials such as Keystore password.
5. Prepare App Store Listing

App listing is a powerful element that helps your application in gaining downloads. Not every one devotes their time on app listing but if you do this before android app submission, you will definitely see some mind-blowing results.
In the app listing, you provide some information to users about what type of application it is and what are its features. One of the best practices of app listing is using high-quality screenshots. Play Store requirements allow developers to use a maximum of 8 images and a minimum of 2.
Here are the best practices and what you should include in your app listing-
-
- Title
- Short Description
- Full Description
- Screenshots of your app (JPEG or 24-bit PNG)(Min-320px,Max-3840px)
- Hi-resolution icon (512 x 512)((with alpha) 32-bit PNG)
- Feature Graphic (1024 w x 500 h)(JPG or 24-bit PNG (no alpha))
- Type of application
- Category of your app
- Rating of the content
- Email of Developer or Company
- Url for Privacy Policy
6. Go Through Guidelines

When it comes to App Store vs Play Store guidelines, it is safe to say that Google’s guidelines are more flexible, which works in favor of developers.
However, you have to be careful when you add an app to the Play Store and you would have to make sure you follow all the guidelines given by Google, lest your app will be kicked out of the platform. Now, this is something you would want to avoid at all costs, right?
Step-by-Step Process to Upload App To Google Play Store
Now that the obvious is out of the way, let’s move on to the steps regarding how to upload an app on Play Store. Make sure you follow each in the exact chronological order to avoid any mistakes in the process.
1. Google Play Developer Console

In order to upload a mobile app to Google Play Store, a developer dashboard is imperative. Developer console is kind of a backend controlling center, from where developers submit an app to Play Store. There is a one-time fee of $25 by which a developer can open an account, loaded with functions and control features. After paying this one-time fee, you can upload apps to Google Play Store for free.
You need to fill out all the credentials asked while creating the account, such as your name, country and more. Once you submit your account it will take upto 48 hours to get approved.
2. Link Developer Account with Google Wallet Merchant Account

If the app getting uploaded to Play Store supports in-app purchases, then you will need a merchant account. To create one you can sign in to your Google Console account and click on ‘Reports’ followed by ‘Financial Reports’ option. After this, you may select ‘Set up a merchant account now’ option and simply fill out your details.
The merchant account will automatically get linked to your Google Console account and will allow you to manage and examine app sales.
3. Create Application

This is yet another step towards how to publish an app to the play store.
Once you are logged into your developer or publisher account, here are a few steps you need to take:
- In the menu, go to the ‘All applications’ tab
- You will see an option ‘Create Application’ – select it
- From the drop-down menu, choose the application’s default language
- Enter your application’s title (it can be changed later)
- Now, click on “Create”
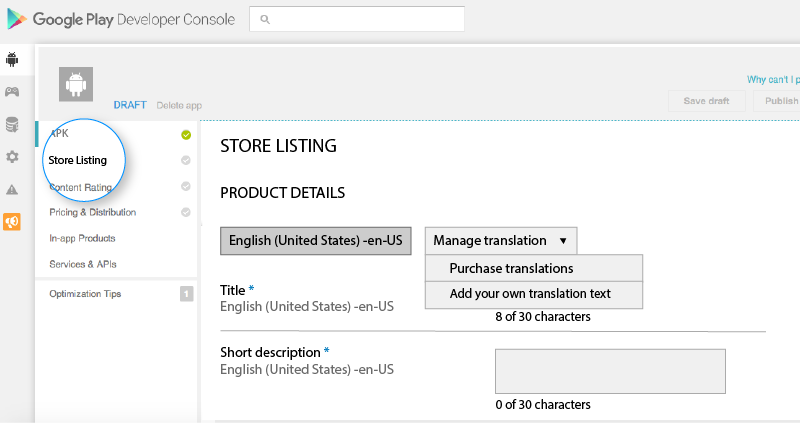
4. App Store Listing

It is at this point, your preparations will come handy.
In this step around how to upload an app to the play store, you are required to fill out all the information and details you have already prepared with caution before. The table below shows what information you need to fill in the app listing-
Make sure to use appropriate keywords in your app description to increase the chances of your app showing up in searches. Along with this, make sure to use all the data we have talked about in the prerequisite section for app listing.
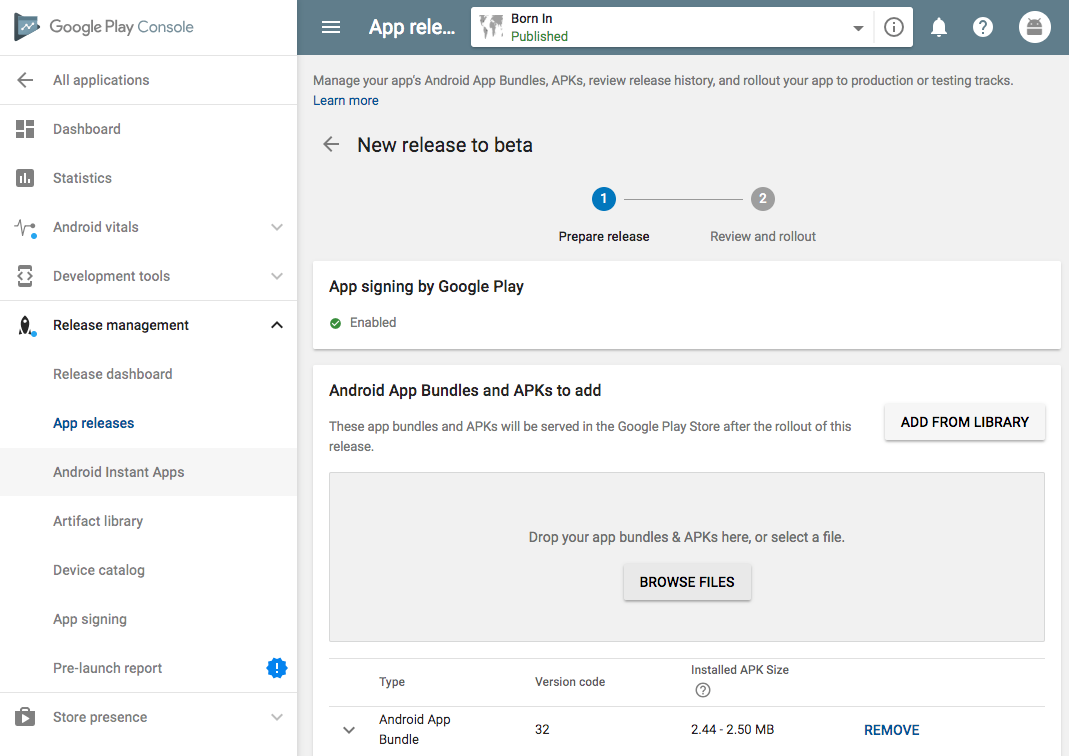
5. Upload App Bundles or APK To Google Play

Now, you are required to use the files such as App bundle or APK and signed app release and upload them into your application. This is how you do it: Navigate to the ‘Release Management’ and then ‘App Release’ tab in the menu. After this, you will be asked to choose any one type of release from four options- internal test, close test, production release, and an open test.
Once, you have made a decision regarding which type of release you want, you may select ‘Create Release’.
At this point, you will be redirected to the New release to the production page. Here, you are again required to make another decision- to opt for Google Play app signing on the app or not. If you choose the latter, then simply click on the ‘OPT-OUT’ option.
Now, select ‘Browse files’ and then look into how to upload apk to google play store while naming and describing your release through on-screen instructions. You can also click on ‘Review’ to confirm the information. When everything is taken care of, press ‘Save’.
6. Time For Content Rating

The next step regarding how to publish apps on the Play Store is to rate your app. This is crucial for it is listed as ‘Unrated’, it might get removed altogether from the store, so it is imperative to rate the application.
For Content Rating, you must again navigate to the menu on the left side of the screen and then select the same. By clicking on ‘Continue’ you can move forward and then type your email address in the respective field and then ‘Confirm’ it.
Now, you may fill the questionnaire for your app rating. Follow this by selecting the ‘Save Questionnaire’ and then choose the ‘Calculate Rating’ option to see your app rating on the Play Store. The last thing to finalize your app’s content rating is to click on ‘Apply’.
7. Fix App Pricing and Distribution

Now, you have to be clear about what countries your app is going to be available in. The point to note here is that Google doesn’t support publishing an app for all regions. The app will be published in selected countries instead of world-wide.
Moreover, assigning a price to your app is crucial. If you want your app to be free, make sure that this decision is permanent, as Google does not allow you to convert free apps into paid ones. Although, the price of the app can be altered.
To do all this, go to the Pricing and Distribution tab in the menu, and then make a choice whether your app is going to be Free or Paid. You may now select the countries you want your app to be released. Additionally, if your application is suited for children under the age of 13, you may select the option of ‘Yes’ for Primary Child-Detected. If otherwise is the case, simply select ‘No’. Similarly, select the options for allowing ads into your application.
8. Finally, Publish the Application

Once you are confirmed about everything being correct, take the last step of this guide on how to upload an app on Play Store, i.e, add the application to the platform. You need to go back to the ‘App Releases’ tab and then select ‘Manage Production’ followed by ‘Edit Release’. After this, click on ‘Review’ and then choose ‘Start rollout to production’ option. To bring this process to an end select the ‘Confirm’ option and Voila! You have successfully uploaded the app to the Google Play Store for free.
All there is left to do now is to just wait for your application to get approved. It generally took about two hours for your application to get reviewed. But with Google Play’s updated privacy policy, it will now take hours and even days for the same, encouraging mobile app development companies to create even more flawless applications that get selected instantly. So, hold your excitement in the place and just wait.
How To Get Your App Featured On Play Store?

Your job to make sure the app gains popularity and thousands of downloads doesn’t end here. After successful execution of the steps regarding how to upload an app to Google Play Store, it is now time to get it featured on Play Store.
There are certain practices such as user interaction and visual design services, working on the latest technologies, localization, etc. that helps your app to get featured. Getting featured on Google Play can benefit your app to an extent that it increases the attention of users on your app by multi-folds.
What To Do After Play Store App Submission?
With the question of “How to publish an app on Play Store” answered, you might think “What is there to do next?”. Well, we have got you covered with this as well. Here are some practices you can do to ensure your application enjoys global exposure.
1. Promote App On Social Media

Social Media is a great medium to skyrocket the popularity of your application. The fact that 42% of the world’s population uses social media is enough to justify the statement. There are some platforms such as Facebook, Instagram, Linkedin, Pinterest, and a lot more that are constantly in use. So, promoting your app on these platforms promises more traffic and eventually more downloads.
2. Initiate Press-Release

Press-release is another way through which you can promote your brand. With this, your brand will come into limelight and many publications will cover your app release which will eventually allow your app to reach a wider user base and develop an authentic connection.
A press release that covers the words, attributes and insights of the mobile app developers and application itself has proved to be an incredible app marketing strategy. It is a great example to show users that what they expect is good.
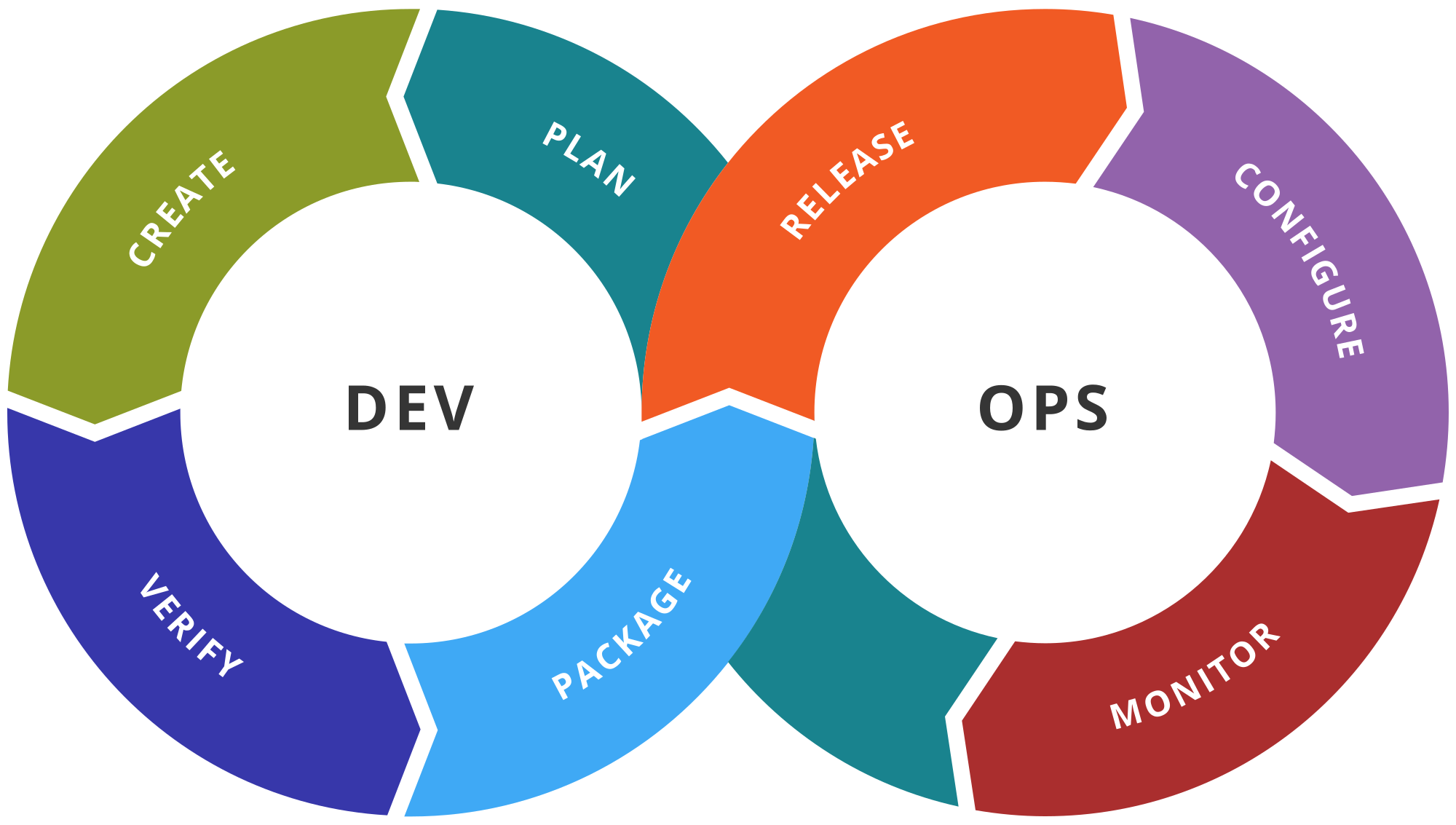
3. Focus On App Maintenance And Update

You cannot just publish your application of the app store and let it be. You need to efficiently maintain your application and introduce frequent updates, attending to the issues and bugs faced by users. Maintaining something is a constant task rather than a one-time thing. So, make sure you keep your app updated with the latest tech-stack and fix whatever needs fixing.
4. Practice ASO

App Store Optimization is a celebrated practice among all the top Android app development companies. Famously known as ASO, it primarily focuses on the activities which target aspects that can generate more attention and visibility of your application of the app store. These practices are focused on increasing the conversion rate of impressions into downloads on the application.




























































:max_bytes(150000):strip_icc()/close-up-of-plasma-light-against-black-background-656332471-582b3d463df78c6f6a94a2e3.jpg)



1555315116314.jpg)



_1554994790.jpg)